ALERT: New Virus Demands Ransom For Your Data
A new type of malware is developing that renders computers unusable until their owners pay a ransom. Worse, the latest example of such ransomware will be sold for as little as twenty-five bucks to anyone who wants easy money. We could be in for a massive wave of cyber-blackmail. Here's what you need to know... |
Ransomware Encrypts Data Until You Pay
Ransomware is not a new concept. The so-called “FBI fine” malware has been around for a few years; it displays a message, purportedly from the FBI or other law enforcement agency, accusing the user of a cyber-crime and preventing any use of the machine until the user pays a “fine” electronically. (See my related article Is The FBI Holding Your Computer for Ransom?)
This type of ransomware does not damage a computer; it only locks a user out. But the latest generation of malware now spreading goes further...
The CryptoLocker virus covertly encrypts all user data on Windows computers with the practically unbreakable Blowfish algorithm, a public/private key encryption method. Affected files include the user's Word documents, spreadsheets, PowerPoint presentations, databases, photographs, and emails.
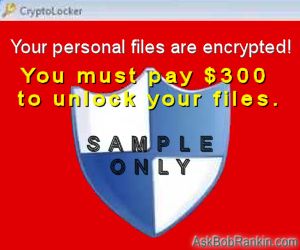
When the encryption process is finished, Cryptolocker displays a message telling the user, “We got ya,” and how to pay a ransom in order to obtain the private key necessary to unlock his/her data.
The scammers will not accept payment via credit card or Paypal, which can be traced to the account owners. They demand payment via anonymous cash services such as Bitcoin or MoneyPak. This makes it harder for authorities to follow the money trail and find the perpetrators.
Cryptolocker was developed and deployed by a small group of cyber-criminals, but it has managed to infect an estimated 250,000 computers since September, 2013. It can attack in a variety of ways, including compromised websites, rogue downloads from file sharing services, and phishing emails that purport to be from your bank, Fedex, UPS, or some other well-known business entity.
A Growing Threat
A new, “improved” version of the same despicable idea is being developed for sale to all comers, which could mean thousands of bad guys distributing an even more destructive ransomware package. Powerlocker, as this malware is called, encrypts user data and also prevents the user from doing anything except interact with the ransom payment screen, a combination of Cryptolocker and the FBI ransomware tactics.
To further limit what can be done with an infected machine, PowerLocker will disable the Alt-Tab, Windows and Escape keys, and prevents the user from running Task Manager, Registry Editor, MSConfig, and Command Prompt windows.
Powerlocker can also detect whether it is being run in a virtual machine or “sandbox,” an isolated area of memory from which applications cannot alter user data. Presumably, this means that Powerlocker will not activate its nasty payload, or will behave in a benign fashion in these environments. This enables Powerlocker to thwart security researchers attempting to safely study the malware.
A group of volunteer “white hats,” security experts who combat malware as a matter of principle, discovered the plot to create Powerlocker while monitoring hacker forums. The group, known as “Malware Must Die” or MMD, published its findings to warn the security software developers and end users of this new, alarming threat.
I will note that so far, all we have is talk about Powerlocker and plans to sell it for as little as $25. No one has seen the ransomware in action. It could be just a bluff, a troll of the security community. But if it’s real, it could be a very big problem.
Preventing CryptoLocker and Similar Infections
What can you do to protect against this threat and others like it? Just keep doing what I have always advised: keep your operating system and anti-malware applications up to date; avoid suspicious Web sites, emails, and other contacts with the online world “out there;” and use common sense when it comes to installing unknown software or opening email attachments from strangers.
You may see products advertised that claim to protect you from Cryptolocker and related threats. But if you're not careful, you could end up installing a "wolf in sheep's clothing" virus that does just the opposite. The good news is that according to VirusTotal, almost all commonly used anti-virus programs will block Cryptolocker from attacking.
The only thing I'd recommend as an extra layer of protection is a little program called CryptoPrevent, which modifies some Windows settings to prevent infection by Cryptolocker and related malware. Note that there are both Free and Premium versions of CryptoPrevent. For information about the program, see this page. You can also go directly to the download for the free version.
If you do get infected by Cryptolocker, Powerlocker or some other virus that attacks by encrypting your files, should you pay the ransom to regain access to your files? Although I've heard that it does work, my advice is no. Doing so only encourages more cybercrime activity. You can either wipe your hard drive and reinstall, or make sure today that you have a complete backup that enables you to restore everything. See my related article Free Backup Software Options to learn how you can get started with a backup strategy.
Your thoughts on this topic are welcome. Post your comment or question below...
This article was posted by Bob Rankin on 14 Jan 2014
| For Fun: Buy Bob a Snickers. |
|
Prev Article: Ten Free Cloud Backup Services |
The Top Twenty |
Next Article: Geekly Update - 15 January 2014 |
There's more reader feedback... See all 27 comments for this article.
Post your Comments, Questions or Suggestions
|
Free Tech Support -- Ask Bob Rankin Subscribe to AskBobRankin Updates: Free Newsletter Copyright © 2005 - Bob Rankin - All Rights Reserved About Us Privacy Policy RSS/XML |
Article information: AskBobRankin -- ALERT: New Virus Demands Ransom For Your Data (Posted: 14 Jan 2014)
Source: https://askbobrankin.com/alert_new_virus_demands_ransom_for_your_data.html
Copyright © 2005 - Bob Rankin - All Rights Reserved



Most recent comments on "ALERT: New Virus Demands Ransom For Your Data"
(See all 27 comments for this article.)Posted by:

Bert
14 Jan 2014
I first ran across an encryption/extortion virus in a malware class at Denver Free University in 1983! Back then, viruses were spread by contaminated 5 1/4" diskettes.
Posted by:

Greg
14 Jan 2014
A few years ago, while staying in a hotel, I asked IT person what software restored the computer upon EVER reboot. He told me Deep Freeze.
http://www.faronics.com/products/deep-freeze/standard/
I seem to recall that user files were untouched, but no windows changes were permanent. Not sure if this would defeat CryptoLocker.
Another idea I have is to always boot from a live Linux CD and then save files to Hard Drive. Again, not sure of effect on Crypto
Posted by:

Don MacDonald
14 Jan 2014
Near the end of your article You have a site that says:
For information about the program, see this page.
I clicked it and a site came up called error 500. It didn't make sense, so I stopped it. I tried again and a site started loading that said waiting for www.foolish*t .com to load. I shut it down. Has your article been compromised?
EDITOR'S NOTE: Nothing wrong... the website is FoolishIT.com (as in Foolish IT). The site is busy and a bit slow right now, but if you try again, it should work.
Posted by:

Thom Gillam
14 Jan 2014
Bob, the anti-malware industry is going about it backwards.
It has been said the best defense is a good offense. Many of these viruses phone home to enable their attack. Instead of building bigger and bigger walls of defensive antivirus (which are ALWAYS going to be less than 100% effective), why not put a software on EVERY computer that will follow that signal back to the malware's server and lock IT up?
Take the fight to them! Nobody would risk trying to infect my computer if the result would be a total shutdown of theirs.
EDITOR'S NOTE: The problem is that most malware is distributed via compromised computers and websites. And those belong to ordinary folks who have no idea what's going on.
Posted by:

Joe
14 Jan 2014
This happened to me with the FBI logo and asking for money. It locked up the computer and I couldn't do anything. I was able to boot up to safe mode. I was then able to restore the computer to a later date and that cured the problem.
Posted by:

David Beglinger
14 Jan 2014
Will it infect external hard drives,too?
EDITOR'S NOTE: Yes, it can. Well, at least it can AFFECT them (by encrypting files). That's why I make an image of my hard drive, store it on an external drive, and then occasionally transfer that image to Dick Cheney's Bunker.
Posted by:

MmeMoxie
15 Jan 2014
Bob ... Thanks so much, for the info, regarding "protection" against this heinous virus or whatever this cyber crime is.
I trust you and your recommendations, so I have already downloaded the CryptoPrevent. I was amazed as to how little the download was ... Reminds me, of the old Assembly Code and for me, that made it a "done deal." I even purchased the Premium version, so I wouldn't have to worry about "updates", plus, I can use my Product Code on ALL Home PCs!!! You just can't beat that. :)
My Hubby is pretty good about NOT clicking on everything or responding to everything, without checking it out with me ... But, I have other family members, that will use his computer and they are not as trust worthy. :)
Posted by:

bb
15 Jan 2014
Bob Price:
CrytoPrevent isn't a program. Well, it is a program, but what it does is to lock the folder where CrytoLocker usually executes by changing the rights of that folder. After CrytoPrevent sets the folder rights, it's done and drops out of memory.
Other legitimate programs may blocked by CrytoPrevent, and indeed if a new CrytoLocker variant changes it's executable folder, it will *not* be blocked.
As Bob says, CrytoPrevent is a general defense against a very specific malware. Your first line of defense is your own behavior, second is an updated AV program.
-bb
Posted by:

LeeD
15 Jan 2014
Thats why I keep a Macrium Reflect image of my hard drive on a USB stick. I can always wipe my hard drive and reinstall my windows operating system.
Posted by:

rich
15 Jan 2014
I think in a couple of comments there is a confusion between the garden variety ransomware which simply locks up the computer, and CryptoLocker which is a far more dangerous and tenacious attack. I have had a couple of FBI-type virus attacks which I managed to cope with on my own, though I subsequently found that several websites such as bleepingcomputer.com offered very hand little programs which could free the computer and let one deal with the attack easily. Scary, but easy to defeat (and basically, I'm a novice). But once CryptoLocker has done its dirty work, the only defence seems to be to have a full image backup of your drive on an outside medium so you can wipe the encrypted drive and reinstall.
Fortunately the whole help community seems to be making a concerted effort to point us to the defence we need, including lots of free stuff, so anyone who listens has little to fear.
Posted by:

Sandman
15 Jan 2014
I wonder if a person got infected how they would go if they ran a Ubuntu Live CD. Would they then be able to access their files then copy them to another location where they are safe. If so they could then format and reinstall or if they have an Operating system image they could reimage.
EDITOR'S NOTE: Sure, you might be able to copy the files, but they would still be encrypted and useless.
Posted by:

IanG
15 Jan 2014
Yes, thanks for your usual exceedingly helpful articles Bob :)
Joe: "This happened to me with the FBI logo and asking for money. It locked up the computer and I couldn't do anything. I was able to boot up to safe mode. I was then able to restore the computer to a later date and that cured the problem".
Did you mean you restored your computer to an earlier date?
Posted by:

LEH
15 Jan 2014
This sounds very much like a variant of the FBI ransomware that has been going around for some time.
EDITOR'S NOTE: ...which is why I mentioned that at the beginning of the article. :-)
Posted by:

Neil
15 Jan 2014
I gave up windows some time ago and use only linux distributions. I have had no problems so far but wonder whether linux is really "immune"
Posted by:

Ken
15 Jan 2014
Hello Bob,
Thanks as usual for your informative emails.
I have just downloaded and installed CryptoPrevent.
If it is this simple to lock certain areas from executing rouge code, why does Microsoft not do so as standard? i.e. Why does it take a free program form an enthusiast to do Microsoft's job for them?
I tried to use LastPass's form fill on this comment form, but it did not seem to work. I will have to investigate whether that is to do with CryptoPrevent or something else.
Thanks again for the newsletters,
Ken Ormson
Posted by:

Ian Atkinson
15 Jan 2014
Comment from one of my very expert adult sons.
One point he should make more clearly is that backups must be 'offline', for instance on unplugged USB drives or on write once disks, because this pest will encrypt any data on drives which are online.
Posted by:

Nigel
16 Jan 2014
A very interesting article - thanks Bob.
It would a real ouch if it came to pass. A question for you, I use a Seagate continuous back up drive. It backs up every changed file as it changes (including the OS), so would it back up an encrypted file as a change or a new file, do you know. If the name of the file is also encrypted would the Seagate program think it's a new file and act accordingly. It seems to me it may be a case where one has to carry out a manual back up as well and then disconnect it from the computer.
EDITOR'S NOTE: I don't know if the filenames are encrypted. But if your backup program keeps multiple versions, you should still be able to recover. I make an image backup weekly, with daily incrementals. I keep the backups for four weeks, deleting the oldest each week. And a copy of my image is stored offsite, as well.
Posted by:

abby normal
16 Jan 2014
Just for your information, this ALERT was on Television, on every Major TV Station, ONE MONTH ago!!! I forwarded the Information to all of my Friends!
EDITOR'S NOTE: Yes, cryptolocker has been in the news, but Powerlocker is just emerging. Also, it wasn't until recently that most of the major antivirus programs had detection capability.
Posted by:

Robbie
02 Jun 2014
I was looking through your site about dsl hacks. Kind of got a little insight, as I am sure my dsl is being hacked as I type. but I have encountered the ransomware nonsense I have/had a worm on my P.c. that was posted as a remote ransomware on the ic3.gov site a dll.host running under the default RD in documents, but have noticed I keep getting hit by Android.Trojan.Koler.A. As I feel this might be the same attacker I can't say for a fact other then he would love nothing more then to see me in prison, A: So I'm not a reliable source to the feds if they ever get their crab together and bust him B: just cause he's an evil puke who has done this to people before. Well the Trojan I thought I'd mention. And well I'll be back. like the site.
Posted by:

Des West
07 Jun 2014
Hi again Bob,
Thanks again for a superb article. I have downloaded it (CryptoPrevent) to my computer.
A while ago, a friends computer was 'locked out' with this type of program, and on research I found a program called "Hit-man Pro" - Is it possible for you to research this and maybe post your expert advise as to is suitability/usability as well?
Cheers again. Recommend your newsletters to all my friends and in fact with posts like this one, I send the WHOLE e-mail to them, I also use the B.c.c - to protect their addresses from being harvested by 'bots'.
Thanks again. Des