Beware of This Clever New Scam
Sometimes security researchers publish information that might better be kept under wraps. That seems to have happened in the case of a Trend Micro blog post about a phishing technique that abuses a popular Internet security standard. Within days, someone was using that technique to trick users into granting access to their Google accounts. Here's what you need to know about OAuth scams... |
What is OAuth, and How Can it Be Abused?
In late April, Trend Micro wrote about a hacker group known as Pawn Storm, which has been active since 2004. Pawn Storm generally targets high-profile political figures; in fact, the group is strongly associated with the Russian government and is known to have targeted members of the Democratic National Committee, the German political party Christian Democratic Union (CDU), the parliament and government of Turkey, the parliament of Montenegro, the World Anti-Doping Agency (WADA), Al Jazeera, and many other organizations.
OAuth (the Open Authentication Standard) is a method of allowing third-party apps to log in to a user’s webmail, social media, gaming, or other service without revealing the user’s password. Instead, the third-party app receives a token from the service that gives it specified privileges. A legitimate example would be a program like UpSafe Gmail Backup http://www.upsafe.com/free-gmail-backup/ which needs access to your GMail account so it can backup your messages.
Service providers are supposed to vet third-party apps before giving them OAuth privileges. But Trend Micro’s blog post says, “Some internet service providers only require an email address and a website for third party applications to use OAuth.” Bad actors who get through service providers’ vetting can do a lot of damage to users. In an OAuth attack, the user might receive an email such as the one below.
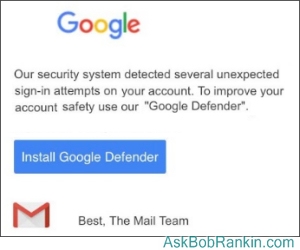
It looks like an official message from Google, and it offers additional safety from a trusted source. Canny users won’t install any software that they didn’t request, but a lot of users will trust Google and click to install “Google Defender.”
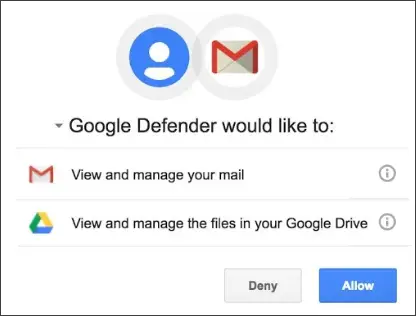
If the user clicks, he will be taken to a screen like the one shown below. This is a real Google-generated page; looking for anomalies in the URL won’t tip off the user. If the user authorizes “Google Defender” to access his mail and Drive files, the bogus app can harvest contacts, sensitive mail, and files stored on Google Drive.
Pawn Storm specializes in political mischief. But barely a week after Trend Micro’s blog post, someone else started using the OAuth technique to phish a large number of users with a slightly different kind of message.
The victims received an email purporting to be a Google Docs share. When they clicked on the link in the email, they are actually installing an app falsely named “Google Docs.” That app requests access to the user’s contacts; if it is granted, the app instantly spams all of the user’s contacts with an identical message that appears to come from the user. This clever scam was sent to many journalists, and even affected our local school district, which uses Google Docs.
You May Be Using OAuth And Not Know It
Google swiftly cracked down on this phishing attack, blocking the bad actors’ accounts and web sites. But more can pop up at any time, and Google is not the only service provider that uses OAuth.
You may have noticed some sites that let you register or sign in using your Google, Facebook, or other service, instead of creating a new username and password for that site. That's OAuth in action. There's nothing inherently unsafe about doing so, but you should think twice. A fake news or other rogue site could pull the same sort of scam described above.
My policy is to avoid OAuth unless I know the party asking to use it is legitimate. I will register the tedious way instead, creating a username and password and providing a throwaway email address if necessary. Under no circumstances would I grant OAuth privileges to any sender of email that I was not expecting, even if it appears to come from a friend or trusted website.
Apps that have gained access to your online account via OAuth will keep it even if you change the account’s password. Their access is granted by a token, not a password. To terminate an app’s access to your Google account, see my article Google Security Checkup, paying special attention to the section on how to check your account permissions. Review all of the apps that have access. Delete the ones that you aren’t using or that don’t look familiar.
On Facebook, click the little gray upside-down triangle on the top right of the window, select Settings, then click Apps in the left-hand column. Here you can review which apps are connected to your Facebook account, and what information they can access. You can edit or delete permissions for each app.
Your thoughts on this topic are welcome. Post your comment or question below...
This article was posted by Bob Rankin on 15 May 2017
| For Fun: Buy Bob a Snickers. |
|
Prev Article: Can You Live Without This New Gadget? |
The Top Twenty |
Next Article: Do I Need an OUTbound Firewall? |
Post your Comments, Questions or Suggestions
|
Free Tech Support -- Ask Bob Rankin Subscribe to AskBobRankin Updates: Free Newsletter Copyright © 2005 - Bob Rankin - All Rights Reserved About Us Privacy Policy RSS/XML |
Article information: AskBobRankin -- Beware of This Clever New Scam (Posted: 15 May 2017)
Source: https://askbobrankin.com/beware_of_this_clever_new_scam.html
Copyright © 2005 - Bob Rankin - All Rights Reserved





Most recent comments on "Beware of This Clever New Scam"
Posted by:

Jay
15 May 2017
I appreciate the time and effort you spend in publishing your newsletter and I read most of them. They are informative and timely.
Thank you,
Jay
Posted by:

Dennis
15 May 2017
Many thanks for the alert.
Posted by:

Karen
15 May 2017
Thanks for the reminder to check which apps are accessed by Facebook. I removed a few this morning.
Posted by:

David Baker
15 May 2017
Thanks Bob for the useful info! Good day!
Posted by:

Dondi
15 May 2017
A worthwhile reminder that interoperability conveniences introduce their own risks. After being told for decades not to use the same credentials on different websites, now we're offered the short cut of using Google or Facebook credentials to access many other sites. But you're hostage to the intent of the website - entering your Google credentials on a Google website is one thing, but typing them into somebody else's website is inherently risky. Not only are you trusting that the owners of the website are benign, but you're also trusting that the website hasn't been hacked.
Posted by:

Don MacDonald
15 May 2017
I had a visit from the phishermen last night. Chrome bullseye came on site and said chrome needs to be updated. I dumbly clicked on it, then realized that Ninite takes care of my updates. I shut it down, but it was too late. I got an e-mail this morning supposedly from paypal for a receipt for a $57 payment from Netflix. I don't subscribe to Netflix. I called Netflix, they asked me to forward the e-mail to them. I have very few apps on my windows7 PC, so I deleted them. I was unable to delete one called Web Store. The logo looks shabby. I now have to figure out how to get rid of it.
Posted by:

Jonathan Skrine
15 May 2017
In the UK our Health board has just advised doctors to stop opening emails.
This means no repeat prescriptions by email and we have to make appointments to get our meds (luckily by phone with our practice).
I wish the NHS IT 'specialists' would sign up to ask Bob.... if it's more than waxing the wire on the abacus basic IT is beyond them at present.
Posted by:

Jerome
16 May 2017
I read many such ezines like AskBob but no one else caught this - Thanks Bob.
Posted by:

CtPaul
16 May 2017
Just more reasons to stop playing with juvenile and time-wasting social media! Also, after the last time that my e-mail got hacked and every contact received links to an erectile dysfunction site I took the time to severely edit my contact list. I realize that most working adults can't do what I have done, but I have retained only 25 contact e-mails, and none of them would be deceived by phony e-mails claiming to be from me.
Posted by:

PeteFior
16 May 2017
More new reasons not to use Goggle or Facebook! I never have and am functioning very well without them. DuckDuckGo does not track my web surfing and my Mozilla email client removes email from the server upon download. It is best to keep a "low profile" - especially these days!