[ALERT] Latest Ransomware Threats
Ransomware seems to be the darling of bad guys these days. It’s a very direct, powerful technique for extorting hundreds of dollars from a single victim very quickly, or millions of dollars when there are thousands of victims. Let’s take a look at the latest ransomware campaigns and how you can protect yourself from them... |
Ransomware: Detection and Protection
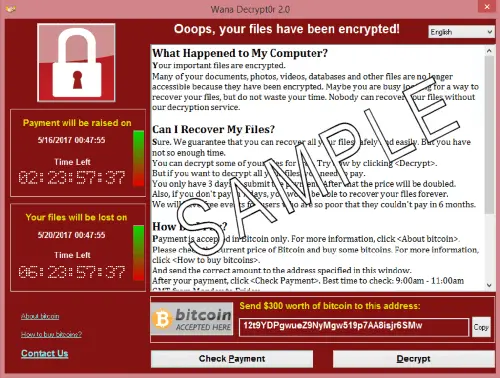
For anyone unfamiliar with it, ransomware is a type of malware that denies a victim access to his or her computer by locking its screen and/or encrypting the files on the hard drive. When a victim tries to access the computer, all they get is an ominous screen like the one below, that says "Oops, your files have been encrypted!"The essence of the deal is, “Pay $X within Y days or you’ll never see your data again.” It’s extortion, pure and simple. But ransomware is getting much more sophisticated these days. The screenshot below comes from the Wannacry ransomware, which infected hundreds of thousand of computers in a single weekend in May.
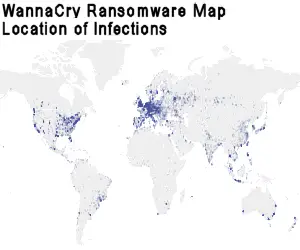
The map shown here was generated by IBM, and shows the worldwide distribution of Wannacry ransomware infections. Apparently, you're safe if you live in Papua New Guinea, Greenland, Niger or Chad. The rest of the world, not so much.
Payment in Bitcoin, the digital crypto-currency, is required. Most victims don’t know much about Bitcoin, so Wannacry and other recent ransomware provide surprisingly good “customer support” to guide victims through the process of creating a Bitcoin account, funding it with real money, and sending money to the extortionist.
One characteristic of Bitcoin is transparency; anyone who knows how can view all Bitcoin transactions since Bitcoin was created. Experts who have examined Bitcoin payments to the creators of Wannacry estimate that this global act of terrorism has so far generated only about $92,000 for its perpetrators. That’s a small return on the infection of an estimated 200,000 computers in 150 countries.
It turns out that Wannacry has a “kill switch” embedded in it that can halt the spread of Wannacry in its track. Within Wannacry’s code is a routine that constantly checks a gibberish domain name to see if it has been registered. As long as the domain remained unregistered, Wannacry would continue infecting any computer it could reach. But when a 22-year-old British security analyst who goes by the handle “MalwareTech” registered that domain, Wannacry stopped trying to spread itself. Amazingly, it cost only $10.69 (the domain registration fee) to halt this worldwide scourge.
That still left hundreds of thousand of computers infected by Wannacry. It’s a mystery how most of them, apparently, have either eradicated the infection somehow or are managing to get by without their data and computers. The UK’s National Health Service is still dealing with the fallout of widespread Wannacry infections on its network, delaying elective surgeries and slowing the nation’s entire health care system to a crawl.
Other Ransomware Attack Vectors
Another new form of ransomware has been dubbed “doxware.” You are unlikely to encounter it because it’s a technique that requires a lot of legwork from the perpetrators. First, they identify high-value targets, computer networks that house highly sensitive, confidential data. Then they infiltrate those networks with ransomware that not only encrypts all files, but also sends to the perpetrators select files that contain words like “confidential,” “top secret,” and so on. Then the victim is told that these files will be posted on a public Web site and all of his contacts will receive the URL that links to that site, unless he pays up by a specified date.
The best defense you can mount against ransomware, or any kind of malware infection, is to keep your operating system up to date with patches for all known vulnerabilities. If you allow Windows Update to run automatically, you should have received the patch to protect against the latest threats.
Microsoft even released a Wannacry patch for Windows XP and Windows 2003, obsolete operating systems that officially no longer receive security updates. Many computers in China, Russia, and even the USA are still running XP, despite its ever-growing vulnerability to hackers and malware. See Microsoft's Customer Guidance for WannaCrypt attacks to read the company's response to WannaCry, and links to those patches.
A good anti-malware suite is also essential, and it must be kept updated too. I use the combination of Avast Antivirus and Malwarebytes Antimalware (MBAM) to provide double coverage. See also my list of Free Anti-Virus Programs for other options.
And of course, be ever-vigilant about opening email attachments. When in doubt, contact the sender to ensure that they actually sent it, and that it's safe to open. Have you or someone you know been affected by a ransomware attack? Your thoughts on this topic are welcome. Post your comment or question below...
This article was posted by Bob Rankin on 26 May 2017
| For Fun: Buy Bob a Snickers. |
|
Prev Article: Geekly Update - 24 May 2017 |
The Top Twenty |
Next Article: Is Kaspersky Anti-Virus Spying for Russia? |
Post your Comments, Questions or Suggestions
|
Free Tech Support -- Ask Bob Rankin Subscribe to AskBobRankin Updates: Free Newsletter Copyright © 2005 - Bob Rankin - All Rights Reserved About Us Privacy Policy RSS/XML |
Article information: AskBobRankin -- [ALERT] Latest Ransomware Threats (Posted: 26 May 2017)
Source: https://askbobrankin.com/alert_latest_ransomware_threats.html
Copyright © 2005 - Bob Rankin - All Rights Reserved



Most recent comments on "[ALERT] Latest Ransomware Threats"
Posted by:

Misterfish
26 May 2017
Seems odd to me that Bitcoins have not been obliged to reveal the perpetrator's account details - it is a crime just as money laundering is, but with the additional criminal intent to endanger lives through hitting state health services.
If someone fails to receive surgery and dies as a consequence, that is manslaughter in the furtherance of a crime. Hunt down these evil people and lock 'em up.
Posted by:

WILLIAM DAVIS
26 May 2017
WARNING ! WARNING !
MALWAREBYTES WILL DETECT YOUR IOBIT SOFTWARE NAMED ADVANCED SYSTEMCARE PRO AND THEN MALWAREBYTES WILL DELETE IT 100% !!
I CONTACTED MALWAREBYTES AND THEY DO NOT HAVE ANY WAY TO FIX THEIR SOFTWARE THAT IS REALLY MESSED UP .
BOB PLEASE INSTALL IOBIT ADVANCED SYSTEMCARE PRO ,, SO YOU CAN SEE THAT I AM 100% CORRECT THEN YOU CAN TELL EVERYONE HOW SCREWED UP MALWAREBYTES REALLY IS .
OR MAYBE YOU DO NOT WANT TO ADMIT HOW MUCH MALWAREBYTES REALLY IS ????????
REGARDS
BILL DAVIS
Posted by:

Rick
26 May 2017
Bob: Another informative article, but you failed to include the best defense against virtually all malware - using a Windows Standard User account for day to day activities (like email and web browsing).
Bill Davis: I run Malwarebytes and ASC on 1 computer and recently experienced what you are describing. I simply chose the option to have Malwarewbytes ignore ASC. In other words I have found that they can coexist. In my experience, ASC is a great product.
Posted by:

CJ Russell
26 May 2017
Our office systems were infected on March 28, 2016. I know the date because I spent hours finding every php file and deleting them. I had to delete them from our website, too, and rewrite some of it. Luckily, I was able to recreate most things by going back to a backup version from before the infection. We did not pay.
About a week after that I saw your article about ransomware and downloaded protection. No problems since. Thank you!
Posted by:

Rich
26 May 2017
If get hacked and have a recent backup image can I install it and be all good?
EDITOR'S NOTE: YES!
Posted by:

Doug
26 May 2017
I have used Malwarebytes for almost as long as it has been on the market, both free and paid versions. Recently it has started classifying legitimate software, especially competitors as PUPs and quarantining them. Considering the extent of this activity one can only assume it is by design.
I stopped using the paid version on my three computers and will not recommend it to anyone.
Posted by:

Jay R
26 May 2017
"If you allow Windows Update to run automatically," - Do you mean that I have a choice? And about the hackers?- Where's Dirty Harry when you need him?
I have paid MBAM, and it flags ACS, but it doesn't quarantine without my permission. I wish that it could, or would, learn. Or maybe it's me that needs to learn.
Thank you for another great article, Bob.
Posted by:

Chris Domres
26 May 2017
It is not clear which version of Windows are affected by WannaCry. I searched my Windows 7 Ultimate registry for the SMB1 entry to shut it off. But there is no SMB1 entry even listed. So Is my Windows 7 machine at risk?
Posted by:

TGreer
26 May 2017
I tend to agree with Malwarebytes... I used to like IOBit, but they've become very slimey, with their aggressive marketing and drive-by installations. I put StartMenu8 on numerous client computers, and now they all have a half-dozen other IOBit programs, and constant pop-ups trying to convert them to paid versions. I'd call that "Potentially Unwanted Programs" (PUPs!)
Posted by:

bb
26 May 2017
Rick: Using a Standard User account would NOT have protected you from Wannacry. It executes in user space, not admin space. True, it would only have encrypted your files, but that's bad enough. Any files you can read, it can encrypt.
Some other interesting facts have emerged about Wannacry. First, there is no way the authors can identify a user that has paid up in Bitcoins, they apparently forgot about that bit of code. Or, more likely didn't care. Even paying up doesn't get your file back.
Second, there is a decrypt tool now available, but you have to have *not* shut down or re-booted your computer. The decrypter grabs the key from RAM. That's no help for 99.99% of victims.
WILLIAM DAVIS: IT DOES ABSOLUTELY NO GOOD TO WRITE IN ALL CAPS, IT IS CONSIDERED RUDE AND 'SHOUTING', REGARDLESS OF YOUR MESSAGE.
Posted by:

BobC
26 May 2017
So rude begets rude in return?
Posted by:

Frank
27 May 2017
ASC10 Pro and BitDefender Free (they are working together nicely) automatically alerted me with instructions to download for my system to ward off Wannacry. Working so far...knock wood. Running Win7 Home Edition-64bits.
Another great column, Bob. I rely on you. Posters: you all are great source of info as well. Thanks all.
Posted by:

Karena
27 May 2017
Windows isn't helping much - I have my Win10 machine set to NOT automatically update because I have a metered internet connection - and I can't find any way to manually update my machine! (I get unlimited data from midnight to 5am.) Anyone know how to update Win10 at will?
Posted by:

NB
27 May 2017
Karena,
At the bottom of your screen, at the left end of the taskbar, is a window that says "Search Windows".
Type "check for updates" in that window.
Posted by:

Karena
28 May 2017
NB - Thanks, but I have tried everything obvious. I found the windows update screen, but there is no option to update manually. I tried following the instructions on the Windows website (I'm not home right now - I don't remember and can't really look it up right this second) - I followed through to the point where it said to click on something like "search for updates", but I didn't have that option on my machine. It wasn't greyed-out or anything, it just wasn't THERE.
I tried looking up this problem on the techie-websites - last I found, it wasn't actually possible to do this at all, but that website was not current (it referred to a test version before the official Win10 release). As much as I have Googled this problem, I haven't yet found a solution.
Posted by:

cal67
28 May 2017
For all the people blasting Malwarebytes, the programs you are defending in almost every case exhibit PUP behaviour and are not as good as you think they are. I have tried lots of IOBIT software and none of it makes the difference they claim it does. If software tells you it will or has sped up your computer by 30%, sit back and think about that. The only way your computer will slow down by 30% is malware, not some registry issues, etc. that need to be optimized. I've tested a lot of these with 3rd party programs to test the computer speed, and none has ever made a difference greater than standard statistical deviation. I'll put my money on Malwarebytes every time.
Posted by:

denis
28 May 2017
I have used Malwarebytes on many computers from when it first appeared on the scene and have never had a problem with it. I always found it an excellent tool in my arsenal when I used to service computers as a job.
Posted by:

Eric Williams
30 May 2017
I m into BitCoin, using GladiaCoin. My GladiaCoin has been hacked by some manner of Malware, blocking access to GladiaCoin, demanding I pay 0.600 BTC to regain access. .600 BTC is over $1,000.00. The rest of my Windows 10 computer seems to work OK.
I use a clone Hard Drive pgm for backup. I changed to a recent cloned drive but that was also blocked the same way. My BlockChain wallet is not blocked???
How do I fix this?
Posted by:

Jim
01 Jun 2017
I had my computer files locked with malware but unthinkingly had my external hard drive set to constantly back up. So, the malware took out the computer files and the files on the external hard drive. I then had to delete files on both drives. Back up on a regular basis and then disconnect the external drive or at least have it set to back up on a schedule only.
Posted by:

Karena
10 Jun 2017
Well, I think I have it figured out: from this web page: http://www.makeuseof.com/tag/manage-windows-update-windows-10/
I obtained this link (look for "L-Space_Traveler" in the comments): http://www.wsusoffline.net/
This is for a program that will let you manually download the Windows updates. I did just try it, and I believe it was successful.