ALERT: Serious Internet Explorer Flaw Discovered
Security holes in Web browsers are hardly unusual, and Microsoft’s Internet Explorer has had more than its fair share exploited and exposed. But the latest flaw is a doozy so dangerous that governments are urging users to switch to alternative browsers until Microsoft issues a patch. And it isn’t clear when that patch will be issued. Find out what you must do NOW... |
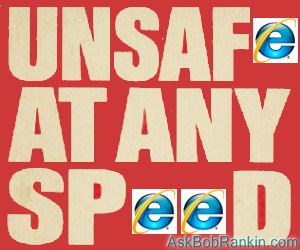
Internet Explorer: Unsafe at Any Speed
The vulnerability, reported by security research firm FireEye on April 26, exists in all versions of Internet Explorer from 6 through 11! Yes, it went undiscovered that long; IE 6 was released in 2001, shortly after the launch of Windows XP. The flaw enables an attacker to bypass IE’s built-in protections against execution of downloaded code and manipulate the browser’s memory space to obtain the same privileges on the affected machine that its user has.
Translation: If you run Internet Explorer, this bug could enable a hacker do almost anything on your computer. That's very bad. And you need to take action right away to protect yourself.
A hacker’s exploit that takes advantage of this vulnerability in IE versions 9 through 11 was discovered by FireEye. Although this specific exploit does not affect earlier IE versions (6, 7, and 8), they are still vulnerable to the underlying flaw. But as Ralph Nader might say, ALL versions of Internet Explorer should be considered "unsafe at any speed" until this problem is resolved.
Here's an even bigger surprise: the fix is available for Windows XP. Microsoft officially ended support for XP on April 8th, and it was expected that XP users would not get a fix for this critical flaw. A Microsoft rep said that due to the proximity of the discovery of this problem to the XP "end of life" date, and the severity of the problem, they decided to issue what is likely to be the final XP patch.
My advice: Make sure you've got Windows Update turned on and running on autopilot. (Open Control Panel, then "System and Security") Also, if you've already switched to an alternate browser such as Google Chrome or Firefox, consider sticking with it, especially if you are clinging to XP.
The malicious code is embedded in a Flash file that may be planted on a Web site. The malware is triggered when a user plays the Flash file. But keep in mind that even if you if you don’t have Flash installed (or you've disabled Flash), the vulnerability still exists and can be exploited in other ways.
Microsoft acknowledge the vulnerability and “a limited number” of instances of its exploitation on April 27. The company promised a fix but did not specify whether the fix will be issued as soon as it’s ready or on the scheduled May 13 “patch Tuesday” when monthly security updates are made available via Windows Update. Note that there is no guarantee that a patch will be ready by May 13.
Also note that Windows XP die-hards will not get a patch for this vulnerability. All support, including critical security updates, for that obsolete operating system ended on April 8. This is the first time that XP users will remain vulnerable to hackers while users of later Windows versions get patches. (See Windows XP: Game Over)
What Steps Should You Take?
Computer emergency response teams (CERTs) in the USA, UK, and Sweden have advised Windows users to avoid using Internet Explorer until a patch is issued. Popular web browsers such as Google Chrome and Firefox are recommended as alternatives to Internet Explorer.
XP and Vista users can reduce their vulnerability by installing Microsoft’s Enhanced Mitigation Experience Toolkit. (Astute readers will remember that I mentioned this tool recently in Free Microsoft Security Tools.) Also, for 64-bit systems running versions 10 or 11 of IE, there is a feature called Enhanced Protected Mode (EPM) that can be enabled to guard against this vulnerability. Instructions for turning on EPM can be found in the Suggested Actions section of Microsoft Security Advisory 2963983.
Security firm Sophos outlines two more mitigation methods for XP users: turning off Active Scripting and unregistering the VGX.DLL file. Step-by-step instructions are provided by Sophos in its bulletin about the vulnerability.
Whatever you do, don’t do nothing. This vulnerability is actually being exploited “in the wild” right now; it is not a hypothetical danger but a real, active one.
Your thoughts on this topic are welcome. Post your comment or question below...
This article was posted by Bob Rankin on 30 Apr 2014
| For Fun: Buy Bob a Snickers. |
|
Prev Article: The End of Free TV? |
The Top Twenty |
Next Article: Geekly Update - 01 May 2014 |
There's more reader feedback... See all 31 comments for this article.
Post your Comments, Questions or Suggestions
|
Free Tech Support -- Ask Bob Rankin Subscribe to AskBobRankin Updates: Free Newsletter Copyright © 2005 - Bob Rankin - All Rights Reserved About Us Privacy Policy RSS/XML |
Article information: AskBobRankin -- ALERT: Serious Internet Explorer Flaw Discovered (Posted: 30 Apr 2014)
Source: https://askbobrankin.com/alert_serious_internet_explorer_flaw_discovered.html
Copyright © 2005 - Bob Rankin - All Rights Reserved



Most recent comments on "ALERT: Serious Internet Explorer Flaw Discovered"
(See all 31 comments for this article.)Posted by:

OldNana
30 Apr 2014
How can I safely download Mozilla Firefox without using IE? If someone downloads the installation file and sends it to me in email or Skype, can I put that on my computer and run it? Thank you for your constant and generous help.
EDITOR'S NOTE: It's safe to download Firefox via IE. The flaw can only be exploited by visiting a compromised website.
Posted by:

Jim
30 Apr 2014
To be clear - just using IE does not put you at risk. You still have to click on a link on a compromised website.
So if you were only using it on known good links you would be safe (which is why using it to download Chrome or Firefox is safe).
However if you casually surf or use Facebook or other sites where people post links that you might follow - you absolutely should not be using it for that kind of behaviour.
http://recode.net/2014/04/27/new-vulnerability-hits-internet-explorer-and-its-serious/
Posted by:

robert
30 Apr 2014
Hi Bob,
Thank you for another one of your invaluable posts!
FWIW, I despise Microsoft. The best description I can assign to them is, arrogance and incompetence in action.
Posted by:

DepOfNville
30 Apr 2014
Is the danger still there if IE is used by an "regular User" account that does NOT have administrative privileges?
EDITOR'S NOTE: To the best of my knowledge, yes. What I read said that an attacker could assume the same privileges as the affected user.
Posted by:

Julie
30 Apr 2014
Hi, is it safe to import my favorites list into firefox? I didn't do it, but it would make my life much easier! Thanks! Couldn't survive without your information!
EDITOR'S NOTE: Yes, that's safe.
Posted by:

pat
30 Apr 2014
Can one just delete the IE off their computor? Since it has internet options etc, is that part of IE?
EDITOR'S NOTE: Because Internet Explorer is a Windows feature, you can't uninstall it. But there's no need anyway, just don't use it.
Posted by:

RandiO
01 May 2014
Since FireFox V29.0 was just released this week, it may be an opportune time to install it in your system. But you also should spend some time to customize it with some "Add-Ons" and "themes" to truly make it a very robust browser. After all, you don't walk out of the house in your skivvies and without some protective add-ons, FireFox is really in the buff!
Posted by:

Daniel Wiener
01 May 2014
I understand the risk of using Windows XP now that it is no longer supported, and in fact I persuaded my daughter to get a new computer a month ago for just that reason, but I don't see what this problem has to do with Windows XP. Presuming that Microsoft gets around to fixing the problem and issues a new safer version of Internet Explorer, why can't XP users just install that new IE version to protect themselves against this exploit?
EDITOR'S NOTE: IE8 is the latest version of IE that you can install on XP. And IE8 is not going to be patched, at least not for XP.
Posted by:

Yves
01 May 2014
Hi Bob, Virus scan like Avast (free edition) is it capable to detect this flaw and fix it?
EDITOR'S NOTE: As I understand the facts, no.
Posted by:

Robert Collie
01 May 2014
The main reason I didn't switch to Chrome until I heard of this ulcer is all my favourites were EI.
Surprize! It is just a click to to import.
I will probably stay with Chrome now because it is not productive to switch back and forth. Familiarity is a big speed enhancer.
Posted by:

Edvins
01 May 2014
Thanks Bob. Much apreciated here down-under as well.
Keep up the good work
Ed
Posted by:

arabgogs
01 May 2014
I love how this is and is always reported like IE and windows are always vulnerable to exploitation.
I wonder if firefox was to really become the most commonly used browser in the world (as opposed to the myth that goes about on certain sites), how long it would take for it to become the main target for exploiters.
Thanks for the update though!
Posted by:

CN
01 May 2014
Since AOL uses IE shold I worry about logging on there?
EDITOR'S NOTE: Years ago, AOL used to distribute a custom version of IE. I think those days are long gone. You can safely access the AOL website and their online services with any browser now.
Posted by:

sandy sutherland
01 May 2014
Hmmm... May have used IE for a few weeks while looking for a replacement browser. I couldn't get away from it fast enough! Netscape was my choice in the 1990s, and Firefox followed when Netscape expired. I suppose many chose to use IE because it was right there in their face, the path of least resistance. There is the possibility some of these internet users are also the least computer savvy, and most at risk.
I am currently exploring Ubuntu. Brother says, "about time!". - 77 and still learning :-)
Posted by:

YSirTinLee
02 May 2014
Just read some good news that includes XP users as well.
http://news.yahoo.com/know-internet-explorer-fix-174420237--abc-news-topstories.html
Posted by:

crimsonsword
02 May 2014
I am also a Tourbus alum. Bob, does using Avant browser which uses IE platform also dangerous? Thanks.
EDITOR'S NOTE: I don't know for sure, but I would think YES. The Avant forums are strangely silent on the issue.
Posted by:

MmeMoxie
02 May 2014
Whew ... This is a biggie!!! Most of us, those who have computer knowledge and have had computers, for quite awhile now ... Know that Microsoft's Internet Explorer - IE - hasn't been the best browser, for a long, long time. Please, I am not getting into the "Browser Wars" issues, either. Microsoft in general, has had many, many multiple security, vulnerable issues, for almost 2 decades. This is one reason, for the routine Microsoft Security Updates, right???
It really has been a long time, since, I have used IE, as my main browser. Mainly, because of all the security issues. BUT ... I do have IE on my computer ... It just comes with the Microsoft Windows Operating System. So, I have taken the precautions, that you mentioned, hoping that Microsoft will have a possible "patch" ... Sometime, in the near future. I do get my "Security Patches" from Microsoft. I totally, adhere to the concept ... An ounce of prevention ... Is better than a pound of cure!!!
Thanks Bob, for giving us several methods, to address this issue. :)
Posted by:

Joe
03 May 2014
Just before I logged on to this site I got an auto update for IE8 and I'm running XP! So, Bob, as of May 2, there's a patch for this on XP.
oh, I know - I'm in process of going to Ubuntu.
Posted by:

MmeMoxie
03 May 2014
Surprise!!! Surprise!!! Surprise!!! I can't believe it, either ... Microsoft, just this EARLY AM ... Updated for the Internet Explorer Flaw!!!
I am totally surprised, just like you were, Bob. This was a BIGGIE, otherwise, MS would have waited, until the next Patch Tuesday. Heavens ... It only took MS 6 days, to make this patch/correction!!!
I thank the stars above, that I DO have my Auto-Windows Update on 24/7, for MS Tuesday Patches. I even had the settings, for MS to go ahead and simply download the patch(es), install them and to restart my PC, if, it is necessary. This way, it was done.
I just happened, to have been on the computer, messing with a game, not working right, that I had just purchased. I had been uninstalling and installing the game ... When, I saw, that there was a "count-down" for restarting the PC. It was then, that I noticed, it was for a Windows Update. I immediately knew, what the update was for. I have been a Windows user, since, Sept. 1996 ... And, I honestly do not ever recall, a Windows Update, on a Saturday morning!!!
As they say ... Try to always be prepared ... You just never know. LOL :)
Posted by:

peter donnelly
12 Apr 2016
my laptop ie, has been frozen by someone, and the site tells me that a graphics crashed/ broken, and gives the phone number
1877-511-2830 for a fix for a fee
how can I report these thieves, and can Microsoft stop them?