Are Password Rules Making Us LESS Secure?
Isn't it maddening when your bank, insurance company, grocery store and a dozen other websites demand that you follow a complicated set of rules when coming up with a new password? It's bad enough that these passwords are hard to remember. But new research shows they actually make it EASIER for hackers to compromise your account. Read on for the scoop… |
Pardon My Password Rant
Normally, when I describe a problem I make sure to also describe a solution. But this problem has no easy solution that you or I can implement. (Well, there is one thing that will help, see below.) So please pardon me while I rant about passwords, security, and the diminishing thereof.
I am sick and tired of password rules that make my life harder and don’t increase my online security. That includes password rules like these:
Password must contain one uppercase letter. Password must contain one lowercase letter. Password must contain one numeric character. Password must contain one special character (!#%, etc.) Password must be 8-10 characters long. Password must contain at least one runic symbol found in the first edition of Lord of the Rings.
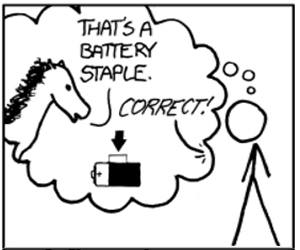
Okay, I made that last one up. But by imposing all of these restrictions, a website narrows a user’s choices, and actually results in LESS security. Here's why… fewer possible passwords makes a hacker’s job easier; his software has to try fewer character combinations before guessing the correct one. So password rules like these actually diminish the security of passwords. One of my favorite cartoons on xkcd.com made this point in a humorous way.
Rules like the ones above also make it difficult to create a password that the user can remember. As a result, users try to satisfy the rules as simply as possible, and end up with a less secure password. I'll bet that a high percentage of passwords created to comply with those rules end up being composed of a common dictionary word, followed by the number 1 and an exclamation point. Does “Monkey1!” (or something very similar) look like a password you've recently used? You can bet that a hacker’s software will try passwords matching that pattern, and sooner rather than later.
These rules can sometimes make it harder to use password manager tools like LastPass, Roboform or Dashlane that automatically generate and remember secure passwords.
Many sites don’t even tell you the rules until you violate them; that’’s extremely annoying when you have just typed a password twice (once to confirm). Similar hidden rules may exist to make you even crazier, like these:
Your password cannot match any of the last five passwords you used. Your password cannot contain your last name. Your password cannot contain your username. Your password cannot contain the name of the current month. Your password cannot be your email address.
We Need Some New Password Rules
The United States National Institute for Standards and Technology (NIST) is formulating new guidelines for password policies to be used by U. S. government systems and sites. “No composition rules” is one of the principle guidelines. NIST has figured out that giving users free rein to create their passwords results in greater security. Hopefully, the private sector will follow NIST’s “best practice” as it often does.
NIST’s guidelines say you need at least 8 characters in a password; that’s in line with most sites’ requirements. But NIST says the maximum password length should be 64, not some arbitrarily skimpy length like 12 or 16. It turns out the length of a password is more important to its security than any other factor.
A large maximum length also enables easily-remembered passwords that are still secure. Take the password, “My_horse_is_named_Ed”. That’s 20 characters. I bet you can remember it more easily than “Xv6Tu!kL,” which is only 8 characters. Yet a 20-character password is orders of magnitude more difficult to crack. The cartoon I referenced above uses the example password "correct horse battery staple" to show that four common words (with no capital letters, numbers or symbols) can be a very secure password.
NIST and private security experts also recommend checking a user’s password against a list of the most common passwords. Everyone knows what those are, including hackers who try passwords like “12345678” or “passwordpassword” before any other combinations.
Like I said, there’s not much the average user can do to revolutionize password composition. But with NIST rolling out sensible guidelines, we may witness the slow death of password rules in our lifetimes. Oh, and I did mention that there's one thing you can do to improve password security. I've been talking about two-factor security for a few years here. See my article An Extra Layer of Security to learn how to lock down your password.
Your thoughts on this topic are welcome. Post your comment or question below...
This article was posted by Bob Rankin on 21 Mar 2017
| For Fun: Buy Bob a Snickers. |
|
Prev Article: [HOWTO] Copy Old Hard Drive to New PC |
The Top Twenty |
Next Article: Geekly Update - 22 March 2017 |
There's more reader feedback... See all 51 comments for this article.
Post your Comments, Questions or Suggestions
|
Free Tech Support -- Ask Bob Rankin Subscribe to AskBobRankin Updates: Free Newsletter Copyright © 2005 - Bob Rankin - All Rights Reserved About Us Privacy Policy RSS/XML |
Article information: AskBobRankin -- Are Password Rules Making Us LESS Secure? (Posted: 21 Mar 2017)
Source: https://askbobrankin.com/are_password_rules_making_us_less_secure.html
Copyright © 2005 - Bob Rankin - All Rights Reserved



Most recent comments on "Are Password Rules Making Us LESS Secure?"
(See all 51 comments for this article.)Posted by:

Mr. Fuji
22 Mar 2017
I'm cancelling all my yahoo email accounts so I don't have to create a new password every time I log in. First they get hacked and don't know it for 2 years...then they go into overkill mode to pretend they have a handle on it. Bye bye YAHOOOOOooooooo.........
Posted by:

john silberman
22 Mar 2017
More and more people are starting to keep a cheat sheet near their PC as well. That seems to make passwords less secure to me as well.
Posted by:

Karena
22 Mar 2017
Marie: I use KeePass - it automatically encrypts the database (I'm sure other password managers do this as well).
Each website still uses a unique password - you only have to remember the master password for your database. Truly, it would be just as secure to make a simple text list of websites and passwords then encrypt that text file - or even keep a printout in a safe location in your own home. It is the convenience of the password manager that I love - I can copy and paste, click and drag, or even auto-fill web-logins. As long as you have one really good secure password (phrase?) to secure your database, you don't really have to worry about it being hacked. Of course, people have different sources of risk - are you at work where someone could literally look over your shoulder? The odds of someone gaining physical access to my home computer are miniscule, and the odds of someone hacking my master password are also. But if you left your password manager open and someone came looking . . . (I know mine can be set to auto-lock after a certain period of inactivity).
One of the big considerations is that if a website gets hacked, a hacker could potentially get your password to THAT site alone, but would not gain anything else (such as your dashlane master password, or any of your passwords to other sites). You can only control security from your end.
Posted by:

Stewart
22 Mar 2017
Banks usually have small print telling you not to write down your password; to do so would mean they would not accept liability if accounts were hacked. Presumably they would consider password manager programs as being 'written down'. And then, of course, they tell us to make a complicated password, and change it regularly. Easier said than done.
Posted by:

Ralph
22 Mar 2017
Your article states: "And of course, these rules make it impossible to use password manager tools like LastPass..." I don't understand your thinking. I've been using LastPass for years, and I can stipulate the password length, use of special characters, etc. It seems to me that a password manager would be ideal in this case. My bank's online site won't accept automatic password insertion, but that's fine. I have a secure note in LastPass that I use to copy and paste. It's worth the extra security to do this for a site I only access once occasionally.
Posted by:

PhilG
22 Mar 2017
Bob the statement "And of course, these rules make it impossible to use password manager tools like LastPass, Roboform or Dashlane that automatically generate and remember secure passwords." is simply false. I've been using Lastpass for years and it generates great passwords based on all said rules. I notice Ralph has had similar results.
Posted by:

Peter Hibbard
22 Mar 2017
Using the usual rules in various combinations, I have remained reasonable secure by including at least one word from a different language. Not a crossover word, like Taco, or a commonly know word like Gracias, but something unusual like tomentosa, (describing the fuzzy nature of some plants, in Latin. If you have a specific ethnic background, use a word from a different language to confuse hackers. So far, I don't believe that hackers have programs that will crack several languages at once in the same password.
Posted by:

Granville Alley
23 Mar 2017
Bob,
I continue to be troubled by your advice regarding the use of common words (even many of them strung together) as virtually all password cracking tools are salted with dictionaries which make passwords made up of words very ineffective to prevent brute force hacking. Particularly since there is an equally easy and far more effective method for creating very secure, very hard to brute force, lengthy passwords that are equally easy to remember. Instead of using the actual words of a phrase My_horse_is_named_Ed, instead use the first letter of each word in the phrase - MhinE add a year for example 1970 and then add another phrase I_Dream_of_Jeanie (IDoJ) for example and to maintain a continuity with your phrase or and_no_one_can_talk_to_a_horse_of_course (anocttahoc) so you end up with a password like MhinE_1970_IDoJ or MhinE_1970_anocttahoc.
Now I personally would use two completely unrelated phrases or song lyrics (the more obscure the phrase and/or song the better) and a historical quote and a number unrelated to either for further obscurity and I end up with an easily remembered by me password and yet one that is virtually impossible to end up in any salted Password Breaking Software Dictionary or for anyone else to guess.
I believe password security best practices support this technique far more than the one you mentioned. I realize this may seem overkill, but Password Cracking Software when combined with salted phrases can reveal many passwords by brute force much quicker than most people imagine possible. 20 Characters is a lot but not when the software can search for recognizable or preloaded patterns or words. Using a common special character to separate words makes the task even easier.
Posted by:

Granville Alley
23 Mar 2017
Just to clarify, when I say makes the task easier, I mean makes cracking the password easier. And when I say using a common special character, I mean repeatedly using the same special character to separate words or phrases.
Posted by:

Randy
23 Mar 2017
One further irritation is when I run into a site that allows you to enter a long password and confirm it. Go to enter it, and bingo! The password is too long to be entered. Guess what? Because the shortened form edition doesn't match the original password on file, you can't log in. If you are lucky, you can get a password reset sent to you, and start over, while remembering the unwritten rules on the web page password entry form!!!!!
Secure order sites have been the worst offenders in my experience.
Posted by:

Keith H
23 Mar 2017
Please clarify you comment about "LastPass" not working. Thanks.
EDITOR'S NOTE: I overstated the case. I was thinking specifically about sites that require the special character to be in a certain position, such as at the end, or ONLY in the middle of the string.
Posted by:

Bruce Fraser
24 Mar 2017
Re: "Password must contain one uppercase letter"
I've only ever seen "must contain AT LEAST one..."
Posted by:

CtPaul
26 Mar 2017
Robert C., thank you for that suggestion. I have not read all the comments here, but it did occur to me that perhaps the overwhelming criticism of both passwords in general and our host's take on the subject indicates that passwords have been rendered obsolete and that all future tech toys that enable you to shop and reach internet sites should now be equipped with retina scanners. (With practice, even a blind person should be able to scan an eyeball, and then use speech recognition software to talk to his/her pc..."
Posted by:

Richard
27 Mar 2017
I would like your opinion on this as an easy to remember password. Let's say you used your father's phone number which is 123-456-7890 but instead of just using the number you use the top row of numbers on your keyboard and hit the shift key every other time (or any pattern you want to use). So your password becomes DaD1@3$5^7*9)
Posted by:

storm
29 Mar 2017
Would using characters that were not on the keyboard slow down the hackers? ☺☻♥♦♣♠•◘○
(These are Alt 1 through Alt 9)
Posted by:

Andy
31 Mar 2017
I totally agree that the new password rules make them less secure! I am totally unable to remember the new passwords multiplied by multiple sites requiring them so I am forced to write them down and store them somewhere.
Posted by:

bob rice
31 Mar 2017
I've seen chats about p/w salts and hashes and tried to understand them. Failed. I am clueless about these terms and what they do,
Posted by:

Frank
03 Apr 2017
Use a passphrase as your core password. It must something that will die with you. It must be something you'll never forget even if you get Alzheimers. And no one else knows about it. You never write it down. It really can be just about any length that is allowed for a password. But the passphrase is accompanied by other letters and/or characters but never meaningful words. Your "cheatsheet ' that you keep beside you omits the passphrase. Other information attached to the passphrase can be remembered and thus provide the security and memorability. I am 99 now and I remember 25 or more passwords easily.
Posted by:

Tony
03 Apr 2017
Regarding LastPass, I don't use it to generate passwords for me, just to store and access what I create myself. Therefore difficult password rules hindering auto-generation, is not an issue for me.
Posted by:

Peter
03 Apr 2017
When it comes to brute force attacks then any upper/lower case letter, number or special symbol is like any other one. It computer terms there is nothing special about a special character, or the case. They are all just numbers representing something the computer doesn't care about.