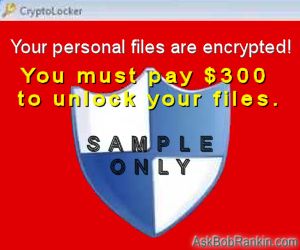
[LOCKED!] The Latest in Anti-Ransomware
Ransomware is the Internet bogeyman of the moment. This breed of malware, which encrypts the data stored on infected machines and then demands a payment for the key that unlocks the data, is the fastest-growing threat online today. The tech press has ensured that awareness of ransomware is at an all-time high. Are you protected? Read on… |
Protecting Against Ransomware
It comes as no surprise that security firms are rolling out anti-ransomware utilities as fast as they can. I wrote about the Malwarebytes Anti-Ransomware utility in January. It was brand-new then, and is still in beta (testing) mode. Other anti-ransomware utilities, all of them free, have joined the fray.
Bitdefender just released a Crypto-Ransomware “vaccine” that prevents installation and execution of certain types of ransomware. The vaccine is an extension of Bitdefender’s CryptoWall vaccine, a one-trick pony that blocked only the CryptoWall ransomware program. The extended vaccine blocks variants of the CTB-Locker, Locky and TeslaCrypt crypto ransomware families. That’s a large group of ransomware, but it’s not all of the possible ransomware threats in existence.
Bitdefender’s vaccine works by detecting a ransomware package’s attempt to check whether the ransomware is already installed on a machine; if that check attempt is observed, the vaccine blocks it and neutralizes the ransomware package. The three families of ransomware mentioned above all have this “check for previous installation” feature.
At first, I thought it was pretty dumb for Bitdefender to tell the world - including the bad guys - exactly how its vaccine detects ransomware. It seems obvious that malware authors can simply omit the check routine and evade Bitdefender’s vaccine. But they probably won’t, because it would be bad for business.
Here's why: If a ransomware program encrypts a drive that’s already been encrypted by another copy of the ransomware program, it will be impossible to decrypt the double-encrypted drive. Victims won’t pay ransoms if it becomes known that doing so will not get their data restored. So the check for previous installations is critical to the bad guys’ business model, and unlikely to be omitted.
More Anti-Ransomware Tools
However, there are less thoughtfully written ransomware programs out there, and Bitdefender’s vaccine won’t stop them. Malwarebytes’ Anti-Ransomware utility employs a variety of behavior analysis methods, probably including the check that Bitdefender uses, to detect and block every known ransomware program.
CryptoPrevent is one of the earliest anti-ransomware utilities. It was released in 2013, in response to the CryptoLocker ransomware threat. Now CryptoPrevent is entering its 8th edition, with more protection against ransomware and other malware threats.
CryptoMonitor is another free utility that claims to protect against all known varieties of ransomware.
There are also tools that attempt to eradicate ransomware infections, with varying degrees of success. If your computer is already infected, try one of these tools.
Trend Micro’s AntiRansomware Tool comes in two versions for two different types of ransomware “scenarios.” “Lock Screen” ransomware simply overlays the victim’s screen with a demand for payment, preventing access to the computer. Crypto ransomware actually encrypts data, and is the more difficult threat to overcome.
The Talos decryptor for TeslaCrypt is an unsupported product of Cisco Systems, created solely to deal with drives encrypted by the TeslaCrypt ransomware program. If you're hit with ransomware and you have no backups, try this before paying good money to bad people.
Your thoughts on this topic are welcome. Post your comment or question below...
This article was posted by Bob Rankin on 7 Apr 2016
| For Fun: Buy Bob a Snickers. |
|
Prev Article: Geekly Update - 05 April 2016 |
The Top Twenty |
Next Article: [TWEAK] Unwanted Windows 10 Features |
There's more reader feedback... See all 26 comments for this article.
Post your Comments, Questions or Suggestions
|
Free Tech Support -- Ask Bob Rankin Subscribe to AskBobRankin Updates: Free Newsletter Copyright © 2005 - Bob Rankin - All Rights Reserved About Us Privacy Policy RSS/XML |
Article information: AskBobRankin -- [LOCKED!] The Latest in Anti-Ransomware (Posted: 7 Apr 2016)
Source: https://askbobrankin.com/locked_the_latest_in_antiransomware.html
Copyright © 2005 - Bob Rankin - All Rights Reserved



Most recent comments on "[LOCKED!] The Latest in Anti-Ransomware"
(See all 26 comments for this article.)Posted by:

Glenn Daily
07 Apr 2016
I clone my computer every night to an external hard drive. I use Acronis but also Reflect I understand is also good. By owning three external hard drives, I always have the last three days of my work available to me.
Posted by:

John Silberman
07 Apr 2016
Just another reason to make frequent back ups.
Posted by:

rReg
07 Apr 2016
Another great article. Thanks, Bob. You are the best.
Posted by:

Joe
07 Apr 2016
Dwayne: Yes, any drive that's mounted in your system and visible to the OS via an assigned drive letter will be accessible to the crypto package. Backup drives must be invisible to the OS to be protected from ransomware. One useful technique is to use a NAS drive for backups that has the ability to schedule its wake time. Make the NAS wake only when a backup is scheduled. Obviously, this technique assumes that you're monitoring the system between backups and will prevent the NAS from waking if an infection occurs.
Posted by:

Debra dew
07 Apr 2016
exactly what you recommend for me to download because I do not download anything unless you say it is safe to do so. I really enjoy reading your opinion, thank you so much all the time you spend helping others.
Posted by:

Jay R
07 Apr 2016
I have installed a program called WinAntiRansom. It has either been working or I have not been attacked. What is your opinion of this one?
Posted by:

Dwayne
07 Apr 2016
Joe, thank you for your input. I am aware that the drives will be visible if they are online: I guess my question is more of "Are the crypto bad guys known to encrypt all visible drives or just the system drive, i.e. C: drive"
Thanks, Dwayne
Posted by:

Al Jankowski
07 Apr 2016
I assume that storing your data in the cloud does not prevent it from being encrypted by ransomware.
True?
Posted by:

John H
07 Apr 2016
I use a timer on my external hard drive, it turn's on when a backup is due. The timer turn's off after the backup is made and the external drive goes to sleep.
Posted by:

bb
07 Apr 2016
For those that want more protection, also look into Microsoft's "EMET", the Enhanced Mitigation Experience Toolkit. https://support.microsoft.com/en-us/kb/2458544. Running as a standard user and having the EMET installed stops most, if not all, of these encrypting viruses.
It also breaks many programs that don't or didn't follow Windows programming recommendations. But that's irrelevant to most of us here.
Posted by:

Foolish Tech
07 Apr 2016
Thanks for the mention of our product CryptoPrevent!
We also wanted to point out v8 beta is now available, if you wanted to check it out, here:
https://www.foolish*t.com/cryptoprevent-beta/
Posted by:

Mike
08 Apr 2016
I still think the silver bullet for any type of malware including ransomware is an image backup. I use Macrium Reflect Standard Edition (64) bit. I do a complete image backup once per week. I have used other image backup programs but Macrium Reflect is the only one that I have been able to do a successful restore every time. I have had to do a restore 3 times in the past 5 years. None do to malware. All 3 times were my fault for tinkering with the OS.
Posted by:

John
08 Apr 2016
Already using the free version of Bit Defender so I downloaded their version. Thank you very much for your article.
Posted by:

Mikey
08 Apr 2016
https://www.winpatrol.com/winantiransom/
Highly recommend...unintrusive and makes good sense
Posted by:

David
08 Apr 2016
CryptoMonitor is no longer valid. The author is now working for Malwarebytes and is producing MB AntiRansomware. It was stated early on in the BETA testing that this software was not going to be a stand alone utility but would be included in Malwarebytes other products.
No matter which prevention software you use, please have an offline (not always connected) backup and keep it current.
When it comes to ransomware, in the end the best thing is you back up, you back up, you back up. Removing the ransomware code is never a problem; recovery of the previous data is.
Posted by:

Therrito
08 Apr 2016
Great article! Does the Ransomware affect only C or can D & E drives be locked up too?
Posted by:

Arcticrose
09 Apr 2016
Thank you. Having had the experience with ransomware, I found a way around it in Windows 10. I just asked Cortana to take me to another site. (She wasn't affected.) I know lucky me.
EDITOR'S NOTE: That doesn't sound like a ransomware attack. When ransomware strikes, your files are encrypted (scrambled) and you're pretty much stuck unless you pay the ransom.
Posted by:

marge201
10 Apr 2016
Bob, I got an email from Malwarebytes tonight urging everyone to buy Malwarebytes Anti-Exploit Premium $25 to run alongside Malwarebytes Anti-Malware Premium, which I have. What's your thought?
Posted by:

John O
10 Apr 2016
Isn't Win 10 just another form of ransom wear? It took a couple of tries to dump the KB3035583. Then it appeared again from the Balmerites as a recommended upload. I hid this one and discovered a remaining process for GWX which I dumped.
They appear hell bent for charging repetitive fees
and forced upgrades. A protracted ransome?
Posted by:

Howard Lewis
02 Jun 2016
I asked Norton if my Norton 360 protects my Windows 7 64-bit PC against ransomware. Answer was yes, and if I have a problem they'll fix it free. I also was told that I needn't look into any of the software recommended here because 360 provides adequate protection. Any disagreement?
EDITOR'S NOTE: You asked a salesperson for Norton 360 if their product is the best? Of course they'll say yes! :-)