The Internet of Insecure Things
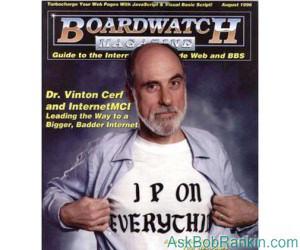
The “Internet of Things,” or IoT, is exploding like a mushroom cloud. Coffee makers, toys, cars, even light bulbs are getting IP addresses and connections to the cloud as manufacturers rush to “add value” to commodity products. But in the mad dash to realize Dr. Vint Cerf’s famous motto, “IP On Everything,” virtually no attention is being paid to securing smart devices against hackers... |
The Connected Future is Looking a Bit Scary
Honeywell Home Automation’s Tuxedo Touch Controller “contains multiple vulnerabilities,” according to a security alert issued by CERT – the Computer Emergency Response Team. “All versions of Honeywell Tuxedo Touch Controller are vulnerable to authentication bypass and cross-site request forgery (CSRF),” says the alert.
That means it’s very easy for anyone to send a command to a Tuxedo Touch Controller that will open doors or unlock windows, turn furnaces or security systems on or off, or tamper with any other device controlled by the Tuxedo Touch. It’s easy to scan the Web and find Tuxedo Touch Controllers, too, much as it was easy (in the early days) for voyeurs to find active Web cameras.
Honeywell released a patch for this vulnerability on July 24. But that doesn’t excuse the company’s failure to design the product right in the first place; the vulnerabilities and how to avoid them have been known for decades. This is what you get when electro-mechanical engineers dabble in Web development.
It’s not just Honeywell that’s been horribly bad at IoT security. Craig Young, security researcher for Tripwire, said in a July 23 media release that he’s found vulnerabilities in the MiOS Vera, WinkHub, and SmartThings Hub that “could allow hackers to identify when people are out of their home, change alarm settings, open locks without authorization, access local area networks and turn smart hubs into zombies,” making them slaves to remote botnet masters.
SmartThings and Quirky, the manufacturer of Wink, quickly issued patches when their mistakes were brought to their attention. But again, the mistakes were rookie mistakes that should never have been made. SmartThings and Quirky pushed the patches out to their devices in consumers’ homes, just as Windows Update automatically delivers security patches. But MiOS doesn’t do automatic updates! Its users have to learn about the danger, locate the patch, and install it themselves. That’s nearly as negligent as not creating a patch at all.
You Think YOU Have Insecurities?
Google’s Nest subsidiary slipped up, too. In March, TrapX Security demonstrated how to hack a Nest Internet-connected thermostat and gain control over other connected devices in a home. That hack required physical access to the device, making it far more difficult than the examples cited above. However, it made buying a used Nest thermostat a risky proposition.
The Nest vulnerability has not been patched, a year after it was first discovered by a University of Southern Florida team led by Professor Yier Jin. “The problem is with the way the hardware is built… Nest can’t repair that,” Jin told Forbes magazine in an interview.
And the problem extends beyond computers, mobile devices and home appliances. A recent Wired story details howhackers took control of a moving Jeep Cherokee from 10 miles away. In this demonstration, a Wired reporter explains how he was powerless to control the air conditioning, radio, windshield wipers, brakes and accelerator, while driving at 70 mph on a highway. The hackers used the cellular connection of the car's Uconnect entertainment system to take complete control of the car. They haven't tried hacking into other makes or models, but I wouldn't be surprised if they are similarly vulnerable.
In a report issued last year, the National Security Telecommunications Advisory Committee said: “…there is a small—and rapidly closing—window to ensure that IoT is adopted in a way that maximizes security and minimizes risk. If the country fails to do so, it will be coping with the consequences for generations.”
Maybe the way to focus manufacturers’ attention on the vulnerabilities of their IoT products is to just stop buying them. Perhaps the Federal Trade Commission can get involved; gaping security holes are certainly indications of a defective, dangerous product. Homeland Security, are you listening?
I don’t know what the solution is, but the problem is serious and growing exponentially. Something must be done to secure the Internet of Things before too many “smart” but insecure devices get embedded in our homes, offices and cars. We need a techno-super-hero here. Maybe Vint Cerf will swoop in and save the day. I'm keeping an eye on the phone booth down the street.
Your thoughts on this topic are welcome. Post your comment or question below...
This article was posted by Bob Rankin on 6 Aug 2015
| For Fun: Buy Bob a Snickers. |
|
Prev Article: Got Windows 10? Do These 5 Things NOW... |
The Top Twenty |
Next Article: Is This the Most Economical Printer? |
Post your Comments, Questions or Suggestions
|
Free Tech Support -- Ask Bob Rankin Subscribe to AskBobRankin Updates: Free Newsletter Copyright © 2005 - Bob Rankin - All Rights Reserved About Us Privacy Policy RSS/XML |
Article information: AskBobRankin -- The Internet of Insecure Things (Posted: 6 Aug 2015)
Source: https://askbobrankin.com/the_internet_of_insecure_things.html
Copyright © 2005 - Bob Rankin - All Rights Reserved



Most recent comments on "The Internet of Insecure Things"
Posted by:

Dave Moran
06 Aug 2015
Feds Say That Banned Researcher Commandeered a Plane
http://www.wired.com/2015/05/feds-say-banned-researcher-commandeered-plane/
Not sure if you want to post this with the potential for people over reacting. This is only one of several articles. One person was put on no fly for just revealing the his ability to monitor flight conditions.
Posted by:

Peter Wall
06 Aug 2015
I really don't care to have a home, car, etc. connected to the internet, ever! The trouble is, the way business works, they don't often give you a "physical" choice to be disconnected, i.e. a fridge that is just a fridge and nothing more, because they can then charge an elevated price for the product even though it's just more parts guaranteed to break down at some point in the future, thus forcing you to buy a replacement, supposedly better, fridge! Or is that a replacement, supposedly better computer, with a fridge attached to it!
Cheers
Posted by:

John Wafford
06 Aug 2015
Many years ago, the then head of Commodore Computers, Jack Tramiel (It might have been Chuck Peddle), when asked if his house was automated, said something to the effect that if his lifestyle was that complicated that it needed a computer to control it, then he'd change his life style.
Posted by:

Jon
06 Aug 2015
I remember my old mum saying that remote controls for TVs would never catch on because there were not enough people who were too lazy to get up to change the channel.
Sometimes I think I have turned into my parents and could be just as wrong.
BUT the internet of things is a bit out there. A recent add tried to get me to buy a kettle that would be activated by an app on my (non-existent) smartphone so I could make tea immediatelly on my arrival home.
Just didn't seem worth the £100++ (USD $150++) to save 5 minutes......
It's a foreign world these days.....
Jon
P.S. Having many American relatives I realise some still don't have electric kettles - they boil about 4to5 USA pints in less than 5 minutes.
Posted by:

Paul
06 Aug 2015
I worked for GM in the mid 80s when they were beginning to include various micro processors in their vehicles. I had a 1986 or 87 Chevy that would open the gate to the underground parking garage where I worked when I drove up to it and a GMC Jimmy that would open my neighbors garage door when I pulled up to mine. That fault was due to poor shielding but the situation is analogous to the slapdash manner in which commercial manufacturers are making smart devices. Look for your digital coffee pot to take control of your house.
Posted by:

Lucy
06 Aug 2015
What about a virus/malware issue when TiVo has access to the secure side of the modem/router?
Is there any concern there?
I don't think I am ready for all these "smart" things to be in our home yet :-)
Posted by:

Reg
06 Aug 2015
As Peter said I'm never buying an appliance or vehicle connected to the internet where the connection's not fully under my control (must be able to easily turn off the connection). Appliances and vehicles can be repaired and the new appliances don't work any better than the old ones. An old stove still cooks the same way. There are even companies restoring old appliances for people who want the "retro" look.
Posted by:

Coos Kid
06 Aug 2015
The recent book Future Crimes by Metcalf has chapter after chapter on these vulnerabilities.
Posted by:

Sandra Hill
07 Aug 2015
Of course the answer is simple. It's not complicated at all! JUST DON'T BUY IT!! Most of us lived without all of these so called "smart" items all of our lives and we don't need them now. Wake up people!!!
Posted by:

Doc
07 Aug 2015
I had the same problem about 40 years ago: a ". . . “smart” but insecure [wife who got]embedded in [my]homes, offices and cars." The fix was pretty simple and I remain single -- if the 'smartest' of the "smart" (quit UC-Berkely after she missed her 10th math problem in her math major [during the second semester of her Junior year])can't meet QA standards, then I fear we are all doomed.
Or we reproduce even newer versions of loT's who share (inherit) many of the same problems, THEN blame our Educational System (and teachers) for allowing them to 'pass' when, clearly, the version 1.0.1 was just, if not even more bug-ridden than the original V 1.0.0 is given the highest praise by V 1.0.0 -- what IS a teacher suppose to do?
We need a solution FAST - before the first v 1.0.1 is allowed anywhere NEAR a teaching credential -- let alone achieves (subsumes) 'unqualified respect of ALL V 1.0.1's by getting that Ph.D. and only the v 1.0.2's know that ALL the 1.0.1's have the fatal flaw that exposes them to be, and able to be controlled by ANY 1.0.2 the paranoid ideas don't seem all that paranoid any more. --
Go ahead and check it out right now - ask ANY 1.0.1 to EXPLAIN why 11 year old 6th graders are crazy - then listen and learn. It's NOT what you think - it's not a software failure, it's a hardware, hard wired problem that was engineered in from the start - and most STILL won't understand even when spelled out THIS clearly.
Heck, ask a simple plain old question we have all had to grapple with at some point in our lives: Please explain and contrast James Joyce's "Ulysses" with William Faulkner's 'The Great Gatsby' using Lewis Mumford's "A History of Time" and incorporate Albert Camus concept that "To insure the adoration of a theorem for any length of time, faith is not enough, a police force is needed as well. (The Plague). You will INSTANTLY see that there is absolutely NO security in ANY loT - at ANY version level - it's a built in flaw - much as DOS has such built in flaws, because it was designed well before any conceivable, imaginable, limit had even been approached.
Since Moores law only applies to things which can occur and be observed only within our own lifetime, the loT version necessary to overcome it's inherent constraint can only be observed AFTER the fall, and never before the fall, of any civilization.
Or so thinks Doc. Please tell me (and explain why) I'm wrong.