When 2FA Goes Bad
Reddit, the maverick social network, suffered a security breach in June, 2018, its management has revealed. It was a mild disaster, as such things go. But it highlights a flawed method of online authentication that you are probably using on a regular basis. Here's what you need to know… |
The Dangerous Flaw in Two-Factor Authentication
Hackers got into Reddit’s internal network and gained access to the cloud-service provider's account credentials of a few Reddit employees, plus “read-only access to some systems that contained backup data, source code and other logs.” No users’ credentials were stolen. But that's the only good news in this story,
This hack spotlights a dangerously flawed two-factor authentication (2FA) technique that is all too commonly deployed by firms that store consumers’ financial, medical, and other sensitive data. Reddit’s investigation revealed the hackers intercepted SMS messages containing codes used to authenticate employees’ login attempts.
Even if you're not acquainted with the jargon, you probably are familiar with SMS-based two-factor authentication. Here's how it works:
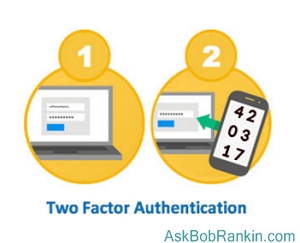
Suppose you try to log in to your bank’s web site. If you must receive a text message and type the code it contains into a form field on the web site, that’s SMS-based 2FA. In two-factor scenarios, the first authentication factor is “something you know," which is usually your password. The second authentication factor is “something you have,” (your phone) by which you receive the text message.
But the SMS (text messaging) protocol is inherently insecure. It is, after all, the Simple Messaging Service protocol, designed from scratch with trivial messages of 140 characters or less in mind. There is no encryption; everything a text message contains can be read by anyone who intercepts the message between sender and receiver. (Just like unencrypted email.)
How Did Reddit Get Hacked?
Don't get me wrong. Two-factor authentication (when done right) is a very good thing. Google and other online services offer 2FA without the insecure SMS requirement. If you turn on this option you’ll need to enter your username/password as usual. You’ll then be prompted for an authentication code before the login can be completed. The code comes from Google Authenticator, an app for your Android or iOS device. This time-sensitive code can be generated even if you’re not online, and you can also print a list of codes for use when you don’t have your phone handy.
None the less, SMS is widespread either as a primary 2FA method or as a backup method should a user be unable to complete authentication via the primary method. Reddit, to its credit, uses a more secure “tokenized” 2FA technique as its primary 2FA method. But Reddit’s cloud service provider(s) did not. (I’ll hazard a guess one of those providers’ names rhymes with “Bamazon.”)
Hackers, partially armed with a Reddit employee’s credentials, were able to fool the cloud service provider into sending them the SMS message containing the 2FA code. With that and an authorized user’s credentials, it was as easy as logging on without any 2FA hurdles.
If you receive 2FA codes via standard email, you may be vulnerable to a similar attack. Email is as unencrypted as text messages unless your email service provider requires a secure connection to its email server. Google GMail and every other webmail service I know requires a secure connection. If you use desktop email software, your email client’s “server settings” should indicate that either TLS or SSL encryption is required.
What You Can Do
Medical practices and other small professional businesses are often not very security-savvy. Even if your doctor requires 2FA for access to his patient portal, it may be SMS-based and therefore very vulnerable. My advice is to show this article to the office manager of your medical practice and urge him/her to ensure that the security protocol used is “HIPAA compliant.”
Geeky jargon may cause the eyes to glaze over, but few things focus medical people’s attention on security like those two words.
Smaller banks and credit unions may also be using SMS 2FA and unaware of its hazards. Run this article by the president or chief information officer, and see what they say. Hopefully a few heads will swivel in your direction.
Your thoughts on this topic are welcome. Post your comment or question below...
This article was posted by Bob Rankin on 3 Aug 2018
| For Fun: Buy Bob a Snickers. |
|
Prev Article: Are You in the 14 Percent Club? |
The Top Twenty |
Next Article: Is Titan the KEY to Your Security? |
Post your Comments, Questions or Suggestions
|
Free Tech Support -- Ask Bob Rankin Subscribe to AskBobRankin Updates: Free Newsletter Copyright © 2005 - Bob Rankin - All Rights Reserved About Us Privacy Policy RSS/XML |
Article information: AskBobRankin -- When 2FA Goes Bad (Posted: 3 Aug 2018)
Source: https://askbobrankin.com/when_2fa_goes_bad.html
Copyright © 2005 - Bob Rankin - All Rights Reserved



Most recent comments on "When 2FA Goes Bad"
Posted by:

Len
03 Aug 2018
Great article!
BTW, I absolutely HATE that floating ad bar that takes up 25% of the page. AND moves as you scroll. AND the X to get rid of it is grayed out.
Please find another way to push ads or as much as I enjoy your articles, I'm gone.
Posted by:

Mat
03 Aug 2018
Len...if you install Adblock Plus, all the ads
disappear.....
Posted by:

Heather
03 Aug 2018
Ok, my credit union uses voice 2 factor authentication, every time. It calls me and I answer and it gives the message. Is that any more secure than SMS?
Posted by:

Bill
03 Aug 2018
Along the lines of Heather's question, is a text message code sent to my phone secure? While email can be easily intercepted, I can't see how a voice or text message could be intercepted after they're sent (maybe before?)
Posted by:

Charles Cochran
03 Aug 2018
I like/hate the method the USAJobs board uses. You enter your password and the system calls you. You answer and the voice on the other end verbally tells you the code. I love that I figure it's secure, but I hate that you must have your phone for access.
Posted by:

G.Wodzien
03 Aug 2018
Thanks for the heads up on flawed (2FA) two-factor authentication.
I use webmail from Gmail and NetZero, they both have,at the address line at the top of the browser a lock/icon followed by "Secure | https:
I hope that is enough.
",your email client’s “server settings” should indicate that either TLS or SSL encryption is required."
The only place I was able to find that is in the email headed . Not all servers are required to show that. Its a can of worms.
see: SOME THINGS TO CONSIDER WHEN MAKING YOUR OWN ANALYSIS OF EMAIL HEADERS FOR ENCRYPTION USAGE
https://luxsci.com/blog/how-you-can-tell-if-an-email-was-sent-using-tls-encryption.html
Posted by:

aa1234aa
04 Aug 2018
I don't see how this failure can be blamed on the 2FA concept. You say "Hackers got into Reddit’s internal network and gained access to the cloud-service provider's account credentials". OK, so hackers stole the login credentials and that's mostly enough by itself. The problem with the Reddit scenario is that it wasn't implementing a 2FA. It was really a 2-step authentication. Just because you ask for 2 pieces of information doesn’t make it a 2FA. Look at how you get into an ATM: you put in your card, which a PHYSICAL item you possess, and then you put in a pin, which is INFORMATION you possess. Two entirely different types of things. With Reddit (or Google or a bank), the “authentication code” sent via SMS or email is another piece of information (same type of thing). If one type of authentication can be hacked, then another item of the same type can also be hacked with the same or similar mechanism. The reason a phone doesn’t qualify as “something you have” is because the access to the phone’s functionality (your phone password, phone number and the SMS) is controlled by information, not the physical thing. Now, if you had some kind of a dongle (e.g. flash drive), and you plugged that into your phone’s USB port, and special software on the dongle verified the SMS code and responded automatically, we’d be getting closed to the intent of 2FA.
Posted by:

Judyth
06 Aug 2018
Further to aa1233aa's point, it seems to me the same applies to a code generated by a Google Authenticator app on one's phone. Anyone who managed to steal the physical phone or socially engineer a SIM "swap" would have the app. Ditto for voice confirmation unless by a real human asking questions or comparing one's responses to a voiceprint.
I do have that pre-issued list of codes to 2FA my Google account, but it's been several years so heaven knows where I put it...
Posted by:

Peterlonz
08 Aug 2018
All very interesting if security is something you value highly.
For most dare I say this discussion will just too much to take in.
At some point the time spent reading & digesting such info becomes a driver for the simple question: so what the heck can I do practically to improve my security on phone & PC?
Suggesting that we present the above to our bank or any other service organisation is plain dopey. You may get a response of sorts but it will not help anyone.