Wireless Security
Is it safe to use wireless Internet access in my home? I've heard that neighbors or even people driving by can tap in to my wireless signal. There must be a way to do it safely, since it's so common these days. Got any tips on wireless security? |
Wireless Taps?
In the last few years, wireless home networks have exploded onto the scene, driven by inexpensive equipment and the desire to set up home networks quickly and easily to access broadband Internet connections. Wireless networks require no drilling and eliminate unsightly cables hanging from the ceiling or tangling under desks.
However, many home users don't realize that by eliminating cables, they are exposing themselves to significant security risk. Cabled networks have an inherently secure feature; only computers physically attached to the network can access the data. Wireless networks, however, are often configured by default to allow access to any computer that attempts to connect to the network. In other words, anyone driving by with a laptop looking for stray wireless signals or anyone with a wireless network card in a neighboring house can use networks configured in that way.
Since wireless networks are so easy to set up, users often don't realize that they are offering free bandwidth to anyone who wants to use it – for any purpose. Obviously, most people would not want to allow their home network to be used for possibly illegal activity, like transmission of child p**nography or spamming. But many don't know how to keep it from happening.
Wireless Security and Encryption
Fortunately, there are two wireless security encryption standards you can use. Wireless Encryption Protocol (WEP) has been around for several years, is supported by all routers and wireless adapters, and provides adequate security for home users. Newer routers and wireless adapters offer the even more secure WiFi Protected Access (WPA), the latest standard in wireless network encryption. If your network router and the wireless adapter in your computer both support WPA, use it. Otherwise, you'll have to use WEP security.
Configuring WEP and WPA
 Since there are many different router manufacturers, and they all have their own setup procedures, it's not possible to cover WEP/WPA configuration for all products. However, we can cover the basics and refer you to the user manual for specifics.
Since there are many different router manufacturers, and they all have their own setup procedures, it's not possible to cover WEP/WPA configuration for all products. However, we can cover the basics and refer you to the user manual for specifics.
The first step is to configure your wireless router to use encryption. (Some routers are shipped with encryption turned off, and some are configured with default passwords that must be changed.) This requires connecting to the router physically (usually using a network cable or USB cable) and setting the security to WEP or WPA following the instructions that came with the router. (Trying to configure the network while connected wirelessly is difficult, because the computer loses connection immediately when the security change kicks in.)
To connect with your router, you'll need to know its IP address. Open a Windows command prompt by clicking Start / Run, then enter CMD and press Enter. When the command prompt window appears, enter the IPCONFIG command. The address shown on the Default Gateway line is the one you want, and is usually 192.168.0.1 or 192.168.1.1 but in any case, your router's manual should tell you the address if you can't otherwise find it. Open your web browser and enter something like this: http://192.168.0.1 (but use the correct address for YOUR router).
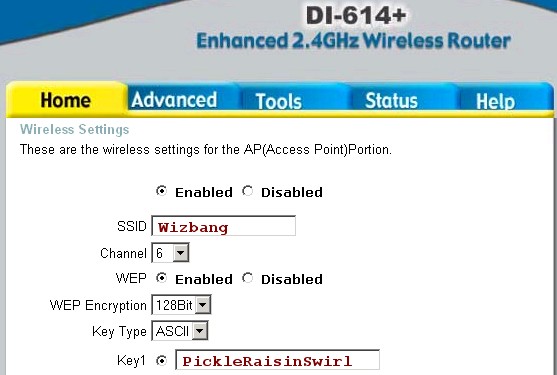
If you don't have the user manual, just poke around in the setup screens to find the right place to change the wireless security settings. In a nutshell, you must supply your own SSID (be creative), make sure encryption is turned ON, and provide a key (password) that any wireless computer will need to connect to your network. Remember, the screenshot above is just an example. If you have a different router, the screen will be somewhat different, but those are the basics. See the screenshot above for a D-Link DI614 router that supports the WEP standard.
Some Notes on WPA Setup
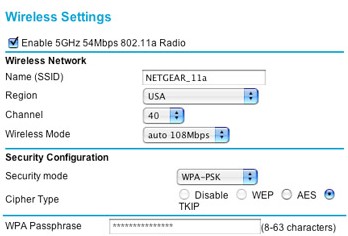 As mentioned before, if your router and your computer's wireless adapter both support WPA, that's the most secure and the recommended way to go. Here's a screenshot for a NetGear router that supports the WPA standard:
As mentioned before, if your router and your computer's wireless adapter both support WPA, that's the most secure and the recommended way to go. Here's a screenshot for a NetGear router that supports the WPA standard:
WPA networks require a password -- sometimes called a passphrase or Pre-Shared Key (PSK) -- that is used to authenticate computers attempting to connect to the network. I recommend that you make your WPA password at least thirty-two characters long and a mixture of uppercase letters, lowercase letters, and numbers to enhance the security of your network.
Note: If your router offers something called Enterprise or RADIUS security, don't go there. RADIUS security is for business networks and requires a separate server on the network to manage security.
Configuring Your Wireless Adapter
Once you have enabled WEP or WPA, selected an SSID, and provided a password, each wireless computer on the network needs to be configured to access the network. Follow the instructions that came with your computer or wireless adapter to set each computer's wireless interface for WEP or WPA encryption and enter the same password that was entered on the router. Windows XP has greatly simplified making a wireless connection, so in most cases you will simply be prompted to enter the security password.
Your wireless computers should now be able to connect to the network and share the Internet connection. If it doesn't work, refer to the troubleshooting instructions that came with the wireless adapter.
Wireless Security On the Go
Is it safe to use wireless Internet access in public places? Two words: Probably Not! If you use wireless Internet access in public places like Starbucks or the airport, you should take some simple precautions to make sure you're not broadcasting your passwords and other personal info to others in the vicinity.
See http://www.askbobrankin.com/is_public_wi-fi_access_safe.html.
This article was posted by Bob Rankin on 23 Dec 2005
| For Fun: Buy Bob a Snickers. |
|
Prev Article: Windows XP Security Tips |
The Top Twenty |
Next Article: Computer Humor |
Post your Comments, Questions or Suggestions
|
Free Tech Support -- Ask Bob Rankin Subscribe to AskBobRankin Updates: Free Newsletter Copyright © 2005 - Bob Rankin - All Rights Reserved About Us Privacy Policy RSS/XML |
Article information: AskBobRankin -- Wireless Security (Posted: 23 Dec 2005)
Source: https://askbobrankin.com/wireless_security.html
Copyright © 2005 - Bob Rankin - All Rights Reserved



Most recent comments on "Wireless Security"
Posted by:

Greg
23 Dec 2005
What about enabling mac addressing, and only allowing computer with specific mac addresses to connect to the router?
EDITOR'S NOTE: That sounds like it should work, even if it is a bit more tedious. But I'm not sure if it's as secure as a WEP/WPA password approach. Anyone know for sure?
Posted by:

David
26 Dec 2005
I believe that MAC addressing is a valid security measure when used WITH an encryption scheme like WEP/WPA. The reason is because MAC addresses can be spoofed, but spoofing the MAC address and crack the encryption would be a task too daunting for an amateur hacker to bother with. Not to mention that even WPA or WPA2 may be cracked someday with a faster computer than what's out now.
My advice: Enable WEP/WPA, and if you know your way around computers, take the extra step of enabling MAC filtering AND (if the router supports it) DISABLE SSID broadcasting. This will keep outsiders from sniffing out your WIFI network from a laptop outside your home or business.
Any one of those measures may protect you, but all 3 plus a good software firewall/antivirus will make your computer network as secure as can be w/o investing thousands for an enterprise security solution.
Posted by:

Nate Hoy
27 Dec 2005
All MAC addresses are transmitted from the client to the WAP (Wireless Access Point) in cleartext. As with "hiding" the SSID, it makes it a little harder for someone to gain access (in that they cannot actually stumble on your network by mistake), but it's a trivial matter to monitor your network traffic with a wireless card and read the headers of all of the packets, and reconstruct valid MAC addresses from the data.
Then all the hacker needs to do is wait until one of your clients disconnects, and connect with its MAC address. So, at the lowest end, to prevent completely casual "accidental" access, disable broadcast of your SSID. One step up, to slow down the really casual network cracker, you can use MAC filtering.
A step above that is WEP security. If you use it, make sure your WEP key is long and complex, and understand that a good hacking program can break it in about 5-10 minutes. Change your key frequently, keep your radio power as low as you can get it and still maintain a connection, and password-protect any servers you have on the WAP.
The next best, by far, is WPA and WPA2. Use a long and complex password to protect against dictionary attacks, and you should be pretty safe. The very best is to use wires. ;)
Posted by:

dj hojo
13 Jan 2006
Thanks for the info! I had WPA and encryption, but after reading this and the comments I went to WPA-PSK, mac address filtering and disabled the ssid.
Posted by:

David A
09 Feb 2006
The more security options you use the less chance anyone can get in on your wireless network. Unfortunately my Nintendo DS only supports WEP otherwise i would only go with WPA. I have WEP, MAC Filtering, Do not Broadcast SSID and finally disable DHCP on router and use an unusual IP range, something like 192.168.3.99 for the router configuration. All this wont stop a determined hacker from reaching your wireless network but unless you have someone local who is hell bent on getting into it you should be safe. Oh and change the router password and encryption key about once a month just in case. It seems daunting to the novice but just take it one step at a time and search on the web for each of the steps... Hope this helps a few people
Posted by:

tomax
01 Mar 2006
Pssst...WEP stands for Wireless Equivalant Privacy, even though I like the netslang version of Wireless Encrypted Privacy. WPA2 is better, but thanks for the tips!
EDITOR'S NOTE: We're both wrong! It's actually "Wired Equivalent Privacy" -- oops.
Posted by:

Avril
12 Dec 2006
how do you hide the SSID?
EDITOR'S NOTE: You have to login to the router with your web browser (usually http://192.168.0.1) and poke around in the security options.
Posted by:

Wayne
11 Jan 2007
Why not spend a few bucks and install Network Magic? It has security features that make locking down your wireless network easy.
Posted by:

chris
10 Aug 2008
I use a Verizon wireless broadband card and live in an apartment complex. I stupidly created an ad hoc wireless network to test transferring a file. Thought better of it and tried deleting it. Couldn't delete it! Since then here's what's been going on. The names and number of names keeps changing in my administrator preferences, dvd-rom tray keeps opening and closing every 10 seconds,will not let me go on a webpage to sign in to my email accounts, both yahoo and gmail. Though ir let me sign up for a @live.com account. I use Norton 360, found nothing. Now I just tried writing to you and halfway thru the page disappeared, so I went offline and am going to try to paste this in fast. I NEED HELP!!!
EDITOR'S NOTE: I recommend you do a System Restore to some date before the problem occurred. That should get you back to good. You might need to remove the broadband card and go offline first.
Posted by:

Charles
13 Oct 2008
Hello Bob, I'm a first time poster to your website. Hope this question is not ask to often. I use desktop PCs everywhere. I was ask by a friend to setup encryption on his wireless LAN. I did so on his router (Linksys N) and setup WEP. On his Laptop PC, he did not have WEP. Where can I go to load WEP to his Dell Laptop?
EDITOR'S NOTE: I could be wrong on this, but I think WPA support must be built into the wireless adapter on a hardware level. You could disable the internal wireless adapter in the laptop, and add a new external adapter which supports WPA. Or just go with WEP. It's pretty robust, unless you have guys in dark sunglasses hanging around.
Posted by:

Duncan
21 Oct 2008
Just a couple of thoughts on WEP and WPA, in the YMMV zone.
My wife has the only Mac in our house (we have two PCs running XP in addition). Due to differences in the way the Mac OS asks/asked for the WEP key in plaintext before scrambling it, we literally can't run WEP as we cannot establish consistent keys across all machines.
On the other hand, although I've tried WPA we had trouble with connections dropping out. I diagnosed this as due to something to do with the key exchange/refresh, after I and colleagues experienced exactly the same happening at work. Both sites have strong signals so that's not the reason.
Posted by:

kylex
20 Apr 2009
Hi there! I was wondering if my provider can trace back the number of users (pc laptop, wifi enabled gadgets) that have accessed our router? and could they possible trace every internet activity as well? i've asked one of their customer service representatives and he said they don't have the information...
EDITOR'S NOTE: It's certainly posible, since by logging into your router, you can see the wifi connections yourself. But I don't know why they'd bother to do so. And if you've changed your router password, that should prevent anyone but you from logging in. As for your internet activity, everything you access is done via the ISP's server. So they COULD log it all...
Posted by:

Rich Madden
22 May 2010
Is there a way that you know of that will let you use a USB Stick to allow temporary access to a wireless network with wpa that would remain on the stick and not get installed onto the laptop, for guests?
Posted by:

lilly adams
17 Jun 2010
The company I used for my Wireless LAN Setup was very knowledgeable and available 24 hours a day for any problems I may have run into. Check out their site http://www.turn-keytechnologies.com. I hope this helps you.