Free Tools for Anonymous Web Browsing
Lately, a number of government figures have declared their opposition to citizens’ use of encryption and other techniques to evade surveillance. Nobody wants the bad guys to win, but the good guys deserve privacy, and in some cases, anonymity. Let's take a look at some free tools that help with that... |
Orwell Was Right, Just 30 Years Early
In George Orwell's classic "1984" an authoritarian government monitors your every word and action. On the heels of recent revelations of government snooping and spying on phone calls, text messages, emails and web surfing, we now have authorities calling foul on tools that are designed to provide privacy and anonymity.
Most recently, the U.S. Justice Department has taken a swipe at Tor, the proxy network that enables one form of anonymous Web browsing. And FBI Director James Comey wants Congress to outlaw “default encryption” on electronic devices and require all providers of encryption services to leave a “back door” through which law enforcement can access a customer’s data… with “appropriate legal authority,” of course.
The problem is that if a back door exists it will be discovered and opened by the wrong people, eventually. That’s why Apple, Google, and other major players are implementing end-to-end encryption that even they cannot decrypt. British Prime Minister David Cameron has made a similar ban of impenetrable encryption an issue in his campaign for re-election. After meeting with Cameron in January, President Barack Obama sided with him and Comey.
The Chinese government “upgraded” its Great Firewall to block all encrypted VPN connections because they are commonly used by dissidents to communicate with each other and foreign sites undetected by government spies. However, VPNs are also used by visiting businesspeople who don’t want their trade secrets stolen by their Chinese “partners.” And of course, VPNs are essential for tourists and journalists who want to speak freely.
Tor, the global proxy network that enables anonymous Web browsing, came under fire from U.S. assistant attorney general Leslie Caldwell on January 27. “We understand 80 percent of traffic on the Tor network involves child p**nography,” she said in an interview. That claim was swiftly debunked by Wired magazine.
Covering Your Tracks Online
If something upsets government snoopers it must be worth knowing; right? So let’s review the state of anonymous Web browsing techniques.
First, we need to distinguish between anonymity and privacy. Privacy is when your activities are unknown; anonymity is when your identity is unknown. I know the people who live in the house across the street from mine; they are not anonymous to me. But I don’t know what they do in the privacy of their home. Conversely, I saw exactly what was done to the tree in my front yard on Halloween but I have no idea who did it because they were disguised; that’s anonymity without privacy.
Anonymity is useful for acting publicly (without privacy) while avoiding consequences, as my neighborhood Halloween vandals knew. On the Internet, anonymity can avert the consequences of government or commercial surveillance. The consequences may be as harmless as creepily targeted ads or as grave as a no-knock raid at 2AM.
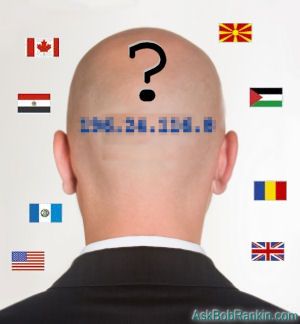
I’ve written about anonymity and privacy tools frequently over the years. My 2011 article, I Always Feel Like Somebody’s Watching Me explains Tor and similar Web proxy services thoroughly. The short story is that a proxy service substitutes its IP address for yours in HTTP requests that are sent to Web sites, and strips cookies and other tracking tools from Web content before passing it back to you. You never interact directly with a Web site so it has no way of learning about you or attaching “bugs” to your browser. There is no record anywhere that you ever visited a particular Web site, let alone of what you did there.
The anonymity of the Web proxy model is not perfect. It is possible to infer “beyond a reasonable doubt” that you were the one downloading copyright-protected movies via a proxy server if your connection to the proxy server, because your IP address is in every exchange of data between your device and the proxy server. If the pattern of traffic passing through your connection to the proxy matches the traffic pattern between the proxy and a server of illegal movies, a government agent can probably get a search warrant. So it is not enough to be anonymous to the Web site that serves you. You also need some privacy; you do not want your IP address or your Web traffic pattern observed.
HTTPS is the First Step
One solution is to encrypt your outbound connection, whether it's to a website you're accessing directly, or a proxy server. If the site you want to reach provides an HTTPS connection, you're all set. The free HTTPS Everywhere browser add-on will try to force an HTTPS connection wherever it’s available.
You can take Web privacy a step further with Tor, which is a network of Web proxy servers and browser software designed for them. When using the Tor browser, your identity and location are obscured and your connection to the Tor network is encrypted. Even your ISP doesn’t know where you’re really going because he can’t read the data stream that passes between you and the Tor proxy server. All anyone knows is that you accessed a Tor server.
Your requests for Web content go to a Tor server, which then reaches out to grab the requested content and relay it back to you over that encrypted connection. The destination site sees the Tor server’s location and ID but never yours. Theoretically, there is no way to tell what you accessed via a Torserver.
Some suspect that the NSA already knows how to crack all existing encryption algorithms. For what it's worth, Ed Snowden says Tor is still beyond the reach of the NSA. But we just don’t know, so you cannot buy certainty at any price.
For most users, making sure you have an HTTPS connection to any site with which you exchange personal or private information should be enough. If your online activities put your life or liberty at risk, then Tor or another proxy service may be worth the trouble.
Your thoughts on this topic are welcome. Post your comment or question below...
This article was posted by Bob Rankin on 12 Feb 2015
| For Fun: Buy Bob a Snickers. |
|
Prev Article: Geekly Update - 11 February 2015 |
The Top Twenty |
Next Article: HOWTO: Connect Your PC to TV, Wirelessly! |
Post your Comments, Questions or Suggestions
|
Free Tech Support -- Ask Bob Rankin Subscribe to AskBobRankin Updates: Free Newsletter Copyright © 2005 - Bob Rankin - All Rights Reserved About Us Privacy Policy RSS/XML |
Article information: AskBobRankin -- Free Tools for Anonymous Web Browsing (Posted: 12 Feb 2015)
Source: https://askbobrankin.com/free_tools_for_anonymous_web_browsing.html
Copyright © 2005 - Bob Rankin - All Rights Reserved



Most recent comments on "Free Tools for Anonymous Web Browsing"
Posted by:

Frank Starr
12 Feb 2015
I had heard that the NSA continually attacks users browsing with TOR. They blast things like untraceable and uneraseable cookies at it, so TOR users are easily tracked by the NSA. Don't know if Mr. Snowden is aware of this, or it may have started after he went into exile.
EDITOR'S NOTE: NSA is blasting untraceable cookies at Tor users? Reference, please?
Posted by:

Louis Toscano
12 Feb 2015
Mr. Rankin's article Mentioning HTTPS Everywhere is especially valuable for those who plan to keep Windows XP and use Firefox as their default browser, IE8 support having ended.
Posted by:

Richard Dengrove
12 Feb 2015
I was told in 1972 that there was no way to stop hackers on computers functioning then, namely minus the net and web. My source was an MIT student studying computers, and it was a matter of logic. Theoretically, no system is impenetrable. All you can do is stop particular gambits.
Posted by:

wes
12 Feb 2015
HTTPS Everywhere cannot be installed in Firefox ;
seems that FF is deliberately blocking it! Come on Bob .. keep abreast of things, seems this extension has been blocked for some time. What gives ?
EDITOR'S NOTE: It's some sort of pi**ing war between EFF and Mozilla. But I found an easy workaround. On the HTTPS Everywhere page, right-click the download link, then select the "Save As" option. Save it to a file on your computer, then drag the xpi file into the Firefox window to install it. Or use File > Open File ... to install it.
Posted by:

Doc
12 Feb 2015
While not a DIRECT reference to TOR I suspect that the Bitcoin CEO's arrest on 27 January 2014 -- whom I am certain,not being a nit-wit, tried to cover his tracks as best he could -- shows oblique evidence that many 'secure' VPNs, are 'open' to at least a few of the few people in dark glasses.
(cite: http://www.washingtonpost.com/blogs/the-switch/wp/2014/01/27/feds-charge-bitcoin-start-up-founder-with-money-laundering/ )
Ref another Bitcoin Exec who used Silk Road: "Silk Road was an online black market that operated using the Tor anonymisation service . ." (cite [Which is also the site] http://www.techweekeurope.co.uk/security/bitcoin-shrem-silk-road-jail-158022 )
So someone was tracking someone -- the inference is that TOR was involved, AND if not mentioned in the above articles, they traced and got him at a public library in NUY. They COULD well have inferred him, then followed, isolated, identified, and then tracked his computer and TOR remains safe.
Posted by:

Carleton Tanner
12 Feb 2015
I always heard that the only truly secure computer was one that was unconnected to a network, unhooked from power and buried at least six feet underground in an undisclosed location.
Posted by:

Alexander Jankowski
13 Feb 2015
Just a note to thank you for asking for a citation for a claim made here. Since then I have noticed citations being provided almost as a matter of course. I feel this will help provide more light and less heat in discussions here.
Posted by:

RandiO
13 Feb 2015
Ironically, there is no https for ebay...
EDITOR'S NOTE: They have it on the checkout page, which, arguably, is the only place it's really needed. But still, why not enable it site-wide?
Posted by:

bb
13 Feb 2015
It’s been a busy time over at the Security Now! Podcast - Steve Gibson had interesting things to say on both the "back door" problem (SN491) and Tor (SN494). Here's a very quick summary:
It was only the media and press reports that used the term "Back door" for allowing the government to read private, encrypted Internet traffic. "Back Doors" are plainly bad as they lower security in an otherwise secure environment. Rightly or wrongly, what people like Cameron wants is another, equally secure "Front Door" available only to government authorized personnel. Technically this is possible; the NSA's Clipper chip in 1993 had such a key escrow system. For example, the master encryption key in an encrypted message could be attached as a message header *twice*, once encrypted with the recipient's public key, and once with the government's public key. Either the recipient's or the government's private key could unlock the message.
Whether that's a good thing to do or not is the readers choice; but technically, it is possible to add multiple "Front Doors" without reducing security. I fully believe that the idea of outlawing encryption is silly, will not enhance our security, and will not catch any more child p**nographers. (Why is it that "they" always yell "child p**n!" and "terrorists!" when they don’t like something?)
Tor (originally developed under a DARPA contract) is showing cracks. Per Gibson, someone with the resources of a nation-state can probably de-anonymize Tor users, and especially if an individual is targeted. Per Snowden, using good encryption *over* Tor makes for pretty good privacy.
Posted by:

John Silberman
13 Feb 2015
A VPN connection insures a secure connection. There are many out there with varying features and very affordable (
Posted by:

Bob McLeran
13 Feb 2015
Be careful if you install HTTPS Everywhere in Firefox - it also installs (but does not activate) a couple of unannounced add-ins that you have to click on and remove from the drop-down menu. Surprised that Bob Rankin doesn't mention that little issue with this add-in. I didn't experience the blocking problem that Wes indicated.
EDITOR'S NOTE: I've chatted with Bob offline. When I installed HTTPS Everywhere in Firefox, I didn't get any unwanted extras. It seems so contrary to the nature of EFF to include foistware in their download.
Posted by:

KW
16 Feb 2015
I've been using HTTPS Everywhere with Firefox for a while, no problems. I seem to be noticing AskBobRankin.com does not enable (or is it allow?) this security, however. Is that correct? I recently noticed the same thing at a medical site which I was required to enroll on, and it gave me a lot of concern.
EDITOR'S NOTE: Typically, one does not need HTTPS (encryption) on sites (such as this one) where you just read the content. But the site is available via HTTPS. You don't even need the HTTPS Everywhere addon. Try this link:
https://askbobrankin.com
Posted by:

Sameer
17 Feb 2015
Any comments about the Tor browser bob.
I do not recall any mention of this web browser in you previous article. Is it reliable and comparable to the major player in browser?
EDITOR'S NOTE: See these links:
http://askbobrankin.com/free_tools_for_anonymous_web_browsing.html
http://askbobrankin.com/beware_the_deep_dark_web.html
Posted by:

Alan M
23 Feb 2015
I may be a worry-wart but....
Any use of anonymous and/or privacy software opens us up as "suspects". This goes on the assumption that if you're trying to hide something you are doing something illegal. With the NSA, that assumption, may be all that is needed to flag you as participating in whatever illegal activity is popular at the moment. They don't have to prove anything, the "Bill of Rights" has no meaning to them. Even if you manage to prove that you are innocent the damage to your life is permanent. The headlines will read "So and So arrested for child p**nography" if you're innocent or guilty that headline remains for ALL to see forever.
Posted by:

Tom
25 Apr 2015
Blur tracking blocker reports: askbobrankin.com 4 trackers blocked. Isn't it a bit Hypocritical to tell people how to surf the web anonymously while you pocket a few bucks to allow tracking beacons on your site to spy on your visitors!
EDITOR'S NOTE: Ummm, no. This is my day job. I make money by publishing a FREE ad-sponsored website. That's no secret, and it's a model that functions as a win-win-win for reader, publisher and merchant. The use of terms like "tracking" and "spying" is misdirection and misinformation, in my opinion. These "trackers" you refer to are just ad networks or social networks. You can block them if you wish, but doing so erodes the ecosystem upon which all free high-quality sites like mine are built.